5 Free Tools To List Third Party Drivers Installed in Windows

Windows drivers are important because a badly coded driver can cause instability and even blue screens of death. Most of the time, a driver file has a .sys extension and a .inf file is often used to install it. Besides Windows already having dozens of drivers installed by default, lots of software can install a driver for both hardware components and to help run the software itself, somewhat like a Windows service.
Drivers can also be used at a low level, such as anti piracy DRM for games and applications, and even malicious programs, such as rootkits. You can, of course, view running drivers in Device Manager. Unused drivers can also be viewed in Device Manager by adjusting a couple of settings. It is not as easy to view drivers that have been installed and are not part of Windows but belong to third party software.
A lot of third party software can leave unused drivers behind which could cause issues affecting your system now or at some point in the future. Below, we list a number of tools that can filter out drivers made by Microsoft or are installed by Windows. This can help narrow down old, unused, or unstable third party drivers you might want to investigate further or remove.
1. Serviwin
Serviwin is a tool we’ve talked about before because in addition to drivers, it can show only third party entries for system services. Serviwin is also a portable tool of only around a hundred Kilobytes in size. Some functions are built in that allow you to start or stop a running driver if you think it might be unneeded or suspicious or change the way it starts up.
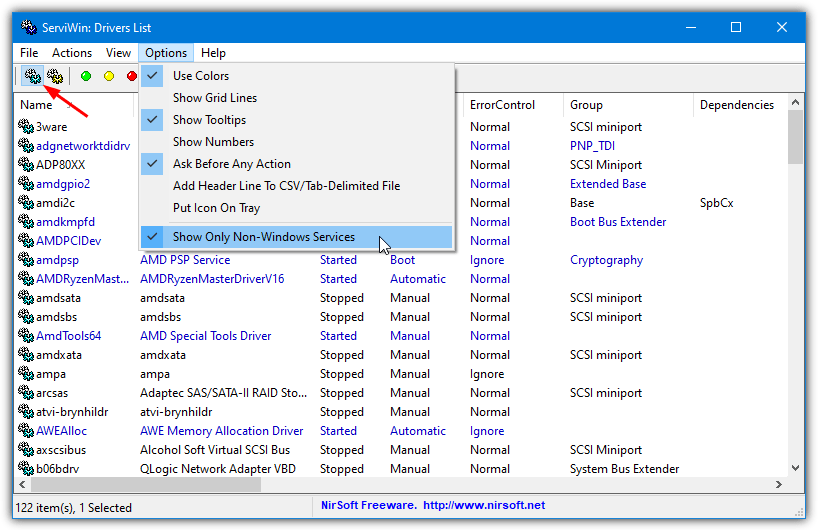
The option to hide Windows drivers and only show those from a third party is turned off by default. Go into the Options menu and enable “Show Only Non-Windows Services” at the bottom. Although the text for the function says services, it works for drivers as well. A lot of information is displayed, double click on a driver to show it in a single window. Serviwin can also pull this data from a remote computer.
2. DriverView
DriverView is from Nirsoft which is actually the same developer as Serviwin above. As a result, both tools share similarities and there is some crossover with regard to what each does. A couple of major differences are DriverView only shows currently loaded drivers (Serviwin shows both started and stopped drivers), and it can be used to monitor drivers in real time and alert you if a driver starts or stops.

There is no ability to start or stop a driver in DriverView but that is not so important for the purposes of listing drivers. An option called “Hide Microsoft Drivers” is found in the View menu and will do what it says, hide any driver that is published by Microsoft. DriverView is portable as well and both tools can export the list of drivers to a text or HTML/XML file.
3. Autoruns
Autoruns is a tool that is made indirectly by Microsoft because the developer Sysinternals is owned by Microsoft. It can display a huge amount of information relating to most things that start with Windows. This includes services, scheduled tasks, media codecs, printers, and drivers. As Autoruns is a portable standalone executable, it’s a hugely popular tool for troubleshooting and diagnosing startup issues.
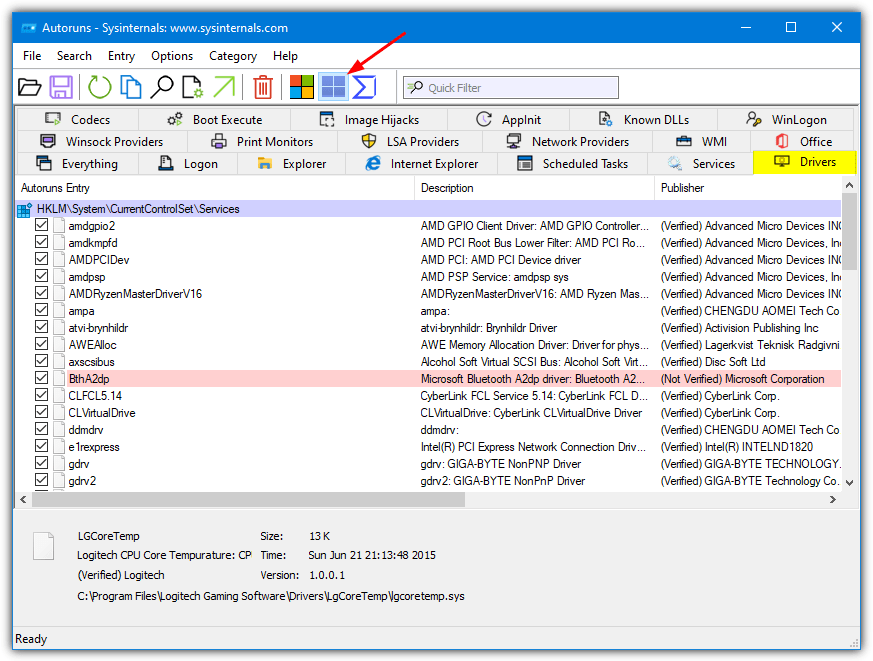
When you click on the Drivers tab inside Autoruns it will already filter out Microsoft drivers. You can reverse this by clicking on the “Hide Windows entries” icon in the toolbar and show everything. There is also a “Hide Microsoft Entries” button but it probably won’t show anything different from the Windows entries button as just about all Microsoft drivers will be Windows drivers.
4. HiBit Startup Manager
As the name might suggest, the primary purpose of HiBit Startup Manager is to display, control, and monitor what is starting up with Windows. Several areas of the system can be checked, including, services, tasks, processes, context menus, and drivers. Unless you know where to look for the driver display window, it can easily be missed. The interface isn’t the best but that doesn’t detract from the program’s usefulness.
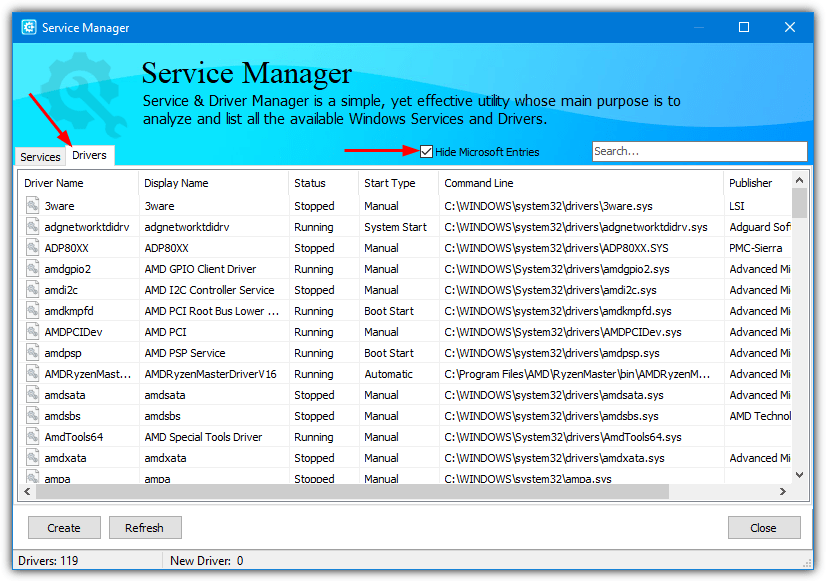
In fact, you need to open the Tools menu at the top right and select Service Manager. There are two tabs, the initial tab is for services but clicking the other will show drivers. Then just check the “Hide Microsoft Entries” box to show only third party drivers. A few extra options like start/stop, delete, and search on VirusTotal are available from the right click context menu.
Download HiBit Startup Manager
5. List Third Party Drivers From The Command Line
In addition to a graphical user interface showing a list of drivers, it could be useful to show all installed third party drivers from the command line. It will be easier using this type of method to perhaps export a list of drivers to a text file for troubleshooting or uploading to an online support forum. Here are a couple of options.
This first option is to use SecurityXploded’s Show Drivers tool. Usage is very simple and you only have to supply a switch to get the required output using an administrative Command Prompt. The options are:
Show all drivers – Showdrivers.exe -a
Show only running drivers – Showdrivers.exe -r
Show only disabled drivers – Showdrivers.exe -d
Show only third-party (Non-Microsoft) drivers – Showdrivers.exe -t
Show more details about a specific driver – Showdrivers.exe -s {driver name}
The “Showdrivers -t” command will be useful for our purposes as it will not show any Microsoft drivers and only those from third parties. The information in the displayed table will be driver name, status, company, description, and driver file path. The “-s {driver name}” switch will be useful to gather more data about an unknown or suspicious entry.

We’d like to have been able to combine switches to for example show only running third party drivers (switches -r and -t), but sadly it’s not possible.
Download SecurityXploded Show Drivers
The second command line tool that can be used is already built into Windows and is called DISM (Deployment Image Servicing and Management). The purpose of DISM is to edit Windows images and it’s quite powerful. A part of its editing ability is being able to add, remove, and service drivers in the image. As a result, there is a command to also list drivers.
Dism /online /Get-Drivers /Format:Table
The above command will show all non Microsoft third party drivers installed on the local system (which is what the /online argument does). The data is displayed in an easy to read table. To show Microsoft drivers as well, just append the “/all” argument to the command.




User forum
0 messages