5 Steps to Investigate and Report Abusive IP Address

Whenever a computer or device connects to an internet or local network, it needs to have a unique IP address assigned to it in that network. The IP address assignment is performed automatically in the background by either your Internet Service Provider if you’re connecting to the Internet, or by an internal DHCP service enabled on a server or a router if connecting to a local network. It acts as an identifier on a network and can be traced back to the device based on the date, time and IP address.
A connection made to any service will expose your IP address to the target. For example, visiting a website using your web browser will initiate a connection from your computer to the web server that is hosting the website. Your IP address will usually be logged by the web server which can be used for analytics traffic reports or even to track abusive behavior such as brute force or DoS attacks.
An IP address isn’t just 4 sets of numbers separated by 3 dotted decimal points. Using the right tools and online services, you can actually find a lot of information about an IP address which can help you to report the attacks to the proper service provider for them to take the necessary actions, such as temporarily suspending the service to prevent further attacks on other targets.
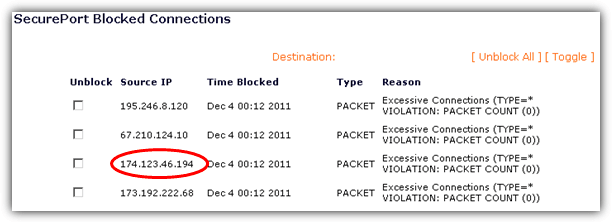
1. Detect Location of IP Address
The most basic information that you can easily get from an IP address is the location. Actually an IP address doesn’t contain any information at all, but yet the location can be revealed by querying a large IP geolocation database that is maintained by different companies, each with different rates of accuracy. One of our favorites is the free online demo version of MaxMind’s Geo2IP City database that includes not only country, but also more detailed information such as subdivisions, city, postal code, latitude and longitude.
All you need to do is enter the IP address into the box and click the Submit button which will instantly output the result on the same page. If you are not satisfied with the results generated by MaxMind’s Geo2IP2 demo, here are 6 more free IP to location alternatives that you can try.
Visit MaxMind Geo2IP2 City Database Demo
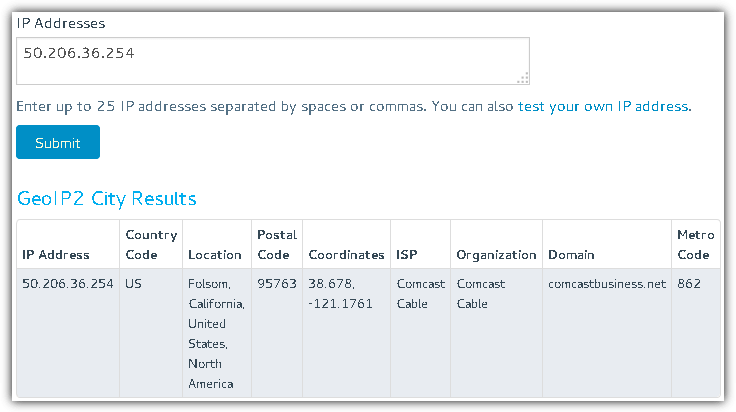
2. Detect Proxy from IP Address
Another piece of important information that you can get from an IP address is by checking if it is running a proxy service. An open proxy is capable of hiding the real user’s IP address so if the attacker’s IP address found in your firewall log is detected as proxy, then there is no need to investigate any further. We’ve found 3 proxy detection services so far that have free web based demos for you to test.
IP Intelligence has launched a free web based checker to detect if an IP address is a proxy or VPN. All you need to do is visit the URL above, enter a valid IP address and click the Lookup button. The results are pretty interesting as it is based on dynamic computation of large data sets. If the system is working, you’ll get a value between 0 to 1.
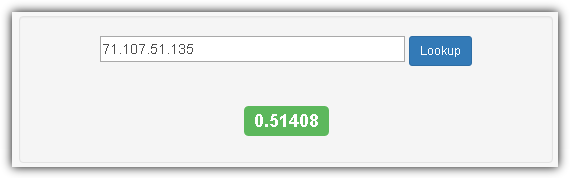
According to their guide, anything above 0.98 are most likely proxies while above 0.90 should be investigated further for confirmation. The screenshot above is an example of an IP address with a pretty low score which is highly unlikely to be a proxy.
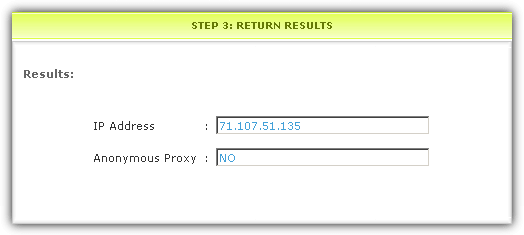
– FraudLab’s IP2Proxy Live Product Demo
A second opinion would greatly help us to confirm if the IP address is indeed a proxy when we couldn’t decide from the IP Intelligence results. FraudLab’s IP2Proxy proxy detection web service allows a maximum of 20 lookups per IP address per day. The online demo can be used straight away without the need to sign up for a free trial account. Enter the IP address in the step 1 box, click Submit and check the results from the step 3 box.
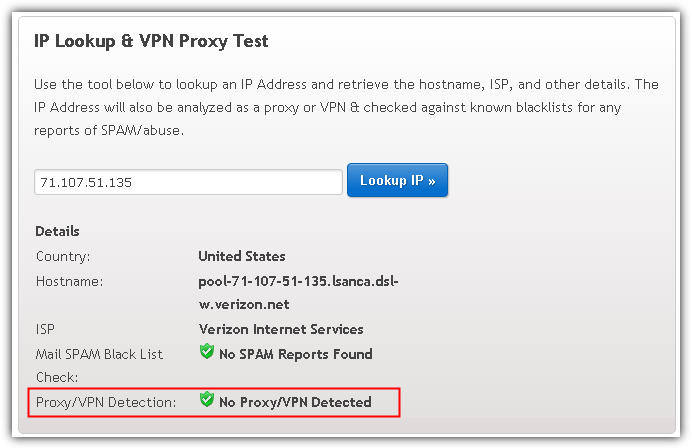
Apart from detecting a proxy and VPN, IPQualityScore has an additional feature to detect a temporary or disposable email address. To perform proxy/vpn checks on an IP address, visit the link above, enter an IP address, click the “Lookup IP” button and refer to the “Proxy/VPN Detection” result. You may need to scroll up to review the results because for some unknown reason the page automatically scrolls down to the bottom of the page.
3. Detect Websites hosted on IP Address
If the computer is running an HTTP web server, the IP address of the server can also reveal the type of websites that it is hosting. A single IP address can actually be configured to host multiple domains which is a method commonly used in shared web hosting. Again, this method relies on checking a database containing domains resolved to IP addresses and the system simply matches the domains that resolve to the same IP address.
This method is known as “Reverse IP Lookup” or “IP neighbor”. There are a number of such services available on the Internet offered for free, but after testing we found only 2 that are quite reliable. They show a good number of updated results while some others still showing domains that do not resolve to the IP address that you’re checking.
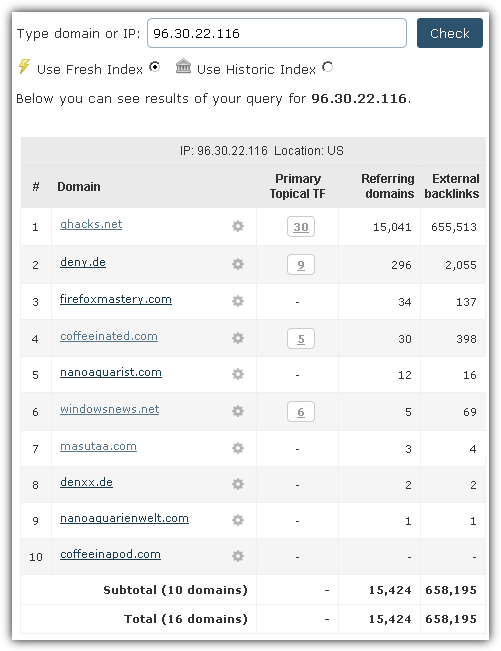
– Majestic Neighbourhood Checker
Majestic is an excellent online tool that is used by a lot of people in the SEO field to analyze backlinks. Since they have their own web crawler that constantly checks for backlinks, it is a no brainer to include results matching domains to IP addresses. All you need to do is enter the IP address in the box, select either to use fresh or history index and click the Check button.
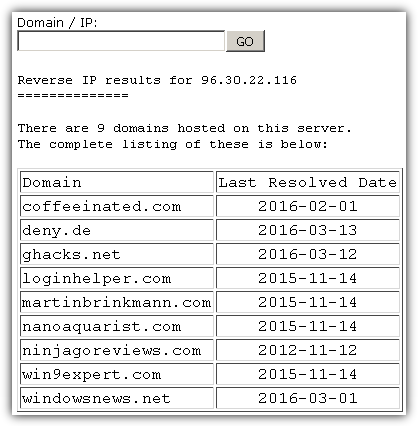
– ViewDNS.info Reverse IP Lookup
ViewDNS.info offers up to 25 online tools for free ranging from a simple online Ping tool to the more complex reverse IP lookup tool. Similar to any other web interface online tool, using ViewDNS.info’s reverse IP lookup tool is as easy as entering the IP address or domain into the given box and clicking a button will reveal the results. In one of our tests, ViewDNS included one of the domain that is missed in Majestic Neighbourhood Checker.
4. Check IP Address for Blacklist
When it comes to checking for blacklists, it is commonly split into two different categories which are spam and malware. You can check the IP address on both categories to find out if it has been used to send spam or host malware.
– MutiRBL
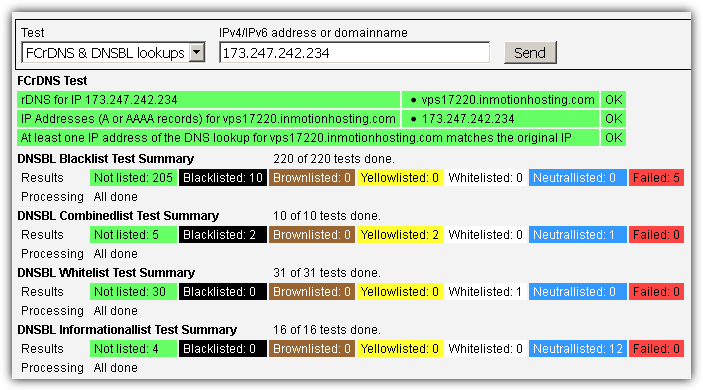
While there are quite a number of free RBL blacklist checkers, we find that MultiRBL is one of the most complete out there that can perform lookups on over 300 RBLs. Simply enter the IP address and click the Send button. The IP address will then be automatically tested on the available DNS-based Blackhole List (DNSBL) or Real-time Blackhole List (RBL).
As for scanning an IP address for malware, there’s also quite a number of IP reputation sources that can check such as Clean MX, Malc0de, Malware Doamin List, SCUMWARE.org and etc. Manually checking each source can be quite troublesome. Fortunately there are some sites that can simultaneously and automatically check multiple IP reputation sources at once.
– IPVoid
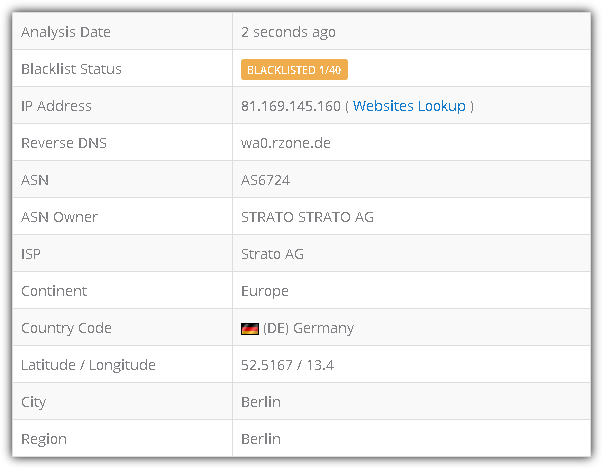
IPVoid is a free IP address scanner service offered by NoVirusThanks. I believe they are aware of the differences in result between scanning URL and IP address which is why they have another service called URLVoid that is meant for scanning URLs, while IPVoid is for scanning IP addresses. IPVoid is able to scan an IP address from 40 different sources that also includes a few RBL checks. Scan results are being cached and if it is showing an old report, simply click the “Update Report” button to initiate a rescan on the IP address.
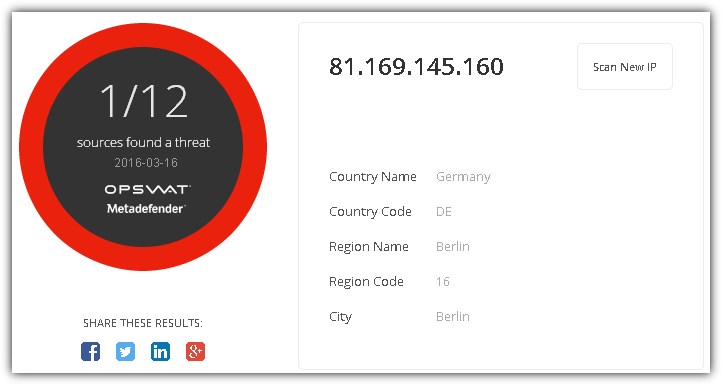
Metadefender is a cloud service that can scan files with 43 different antivirus engines, or scan an IP address from 12 different sources. Unlike IPVoid that includes up to 40 sources, Metadefender is more focused on malware sources and exclude RBL checks.
Additional Notes: We did not include VirusTotal to the list because it doesn’t report the detection for an IP address when one of the engines does flag the IP address as malicious. When we tried scanning a hostname instead, then it shows the detection correctly. This means that VirusTotal URL scanner is meant for a scanning URL, but not an IP address.
5. Reporting Abusive IP Address
After you’ve done all the investigation on the abusive IP address, the last step is to report the malicious activity to the proper authority. You will need to send the firewall log file showing the attack to the abuse email address which can be found by performing a WHOIS on the IP address. One of the most reliable services that can perform a Whois Lookup on an IP address is by DomainTools. Simply type in the IP address and click the Search button which will return a small list of contact information.
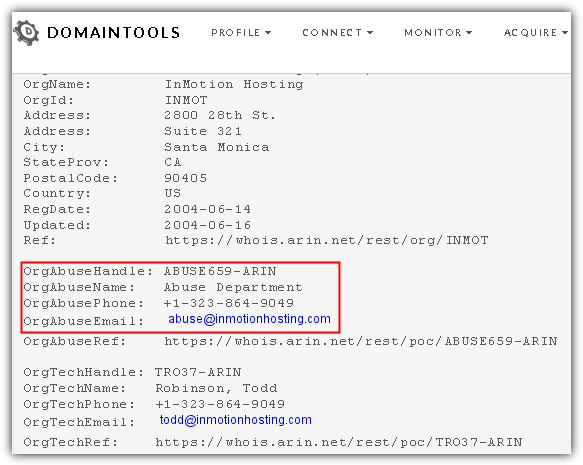
Look for the Abuse department contact information in the whois data. Although the phone number is listed, most likely you’ll still need to email the log files to the abuse department as proof.




User forum
0 messages