10 Websites to Easily Help Decrypt MD5 Hashed Strings

It is common to find websites that allow registration and the login information consisting of username and password is normally stored in the server’s database. Many years ago, passwords stored in database were clear text which is why it is possible to recover lost passwords. This is obviously unsafe because a hacker that manages to hack into the server will instantly have access to thousands of passwords. Other than that, less security minded people will probably use the same password for all online services and this will potentially allow the hacker to gain access to all other services belonging to the user.
To solve this problem, a type of cryptographic hash function called MD5 had been introduced which was deemed safer at that time because it is a one way process. By converting the user’s password to MD5 and storing it on the server’s database, the hacker wouldn’t be able to instantly know your password, even if he managed to access the database. When you login, it simply needs to convert your password that you entered in your web browser to MD5 and compare it in the database. If it matches, then you’re allowed to log in. This also improves the password recovery function by sending a newly generated password rather than allowing you to recover your old password.
Although MD5 is a one way process that cannot be programmatically decrypted, it is still possible to build a database or dictionary file containing MD5 hashes that matches a string because a string will always match the same MD5. For example, the string “password” will always match the MD5 “5f4dcc3b5aa765d61d8327deb882cf99”. MD5 is weak and many online applications such as WordPress no longer store password as MD5 hashes their database.
So is there a way to decrypt MD5? Although not directly, it is possible to perform a reverse lookup. Here are 10 websites containing huge databases that offer online services to check if there is a matching string for a given MD5.
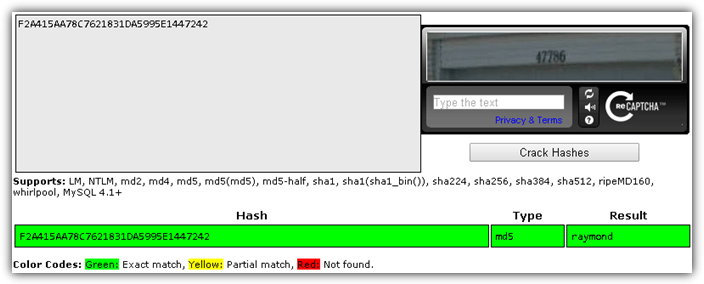
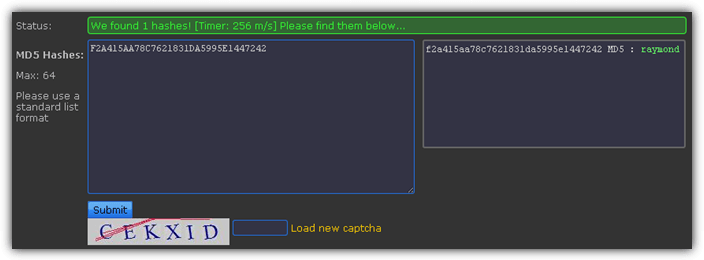
As a simple test, we’ve tried searching a simple MD5 of the string “raymond” and all of them successfully found the string in their database. As for the second round of tests, we appended .cc at the end of the string raymond and only 1 MD5 decrypt service that we’ve listed at the end of this article managed to find the result in their database.
1. md5online.org
md5online.org contains 452 billion words in their database. Other than searching for the original word of the MD5 from the website, you can also request for a batch search which is limited to 100 lines and the results will be sent to the provided email address. They also provide a simple API for paid premium members where their service can be used to decrypt MD5 from a script, website or even application.
2. md5crack.com
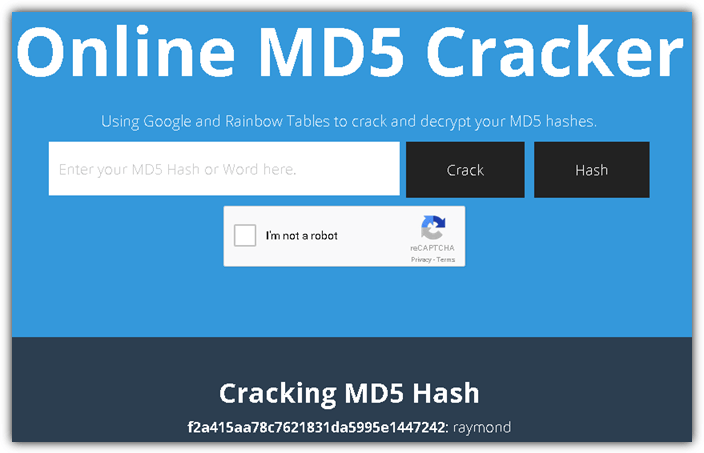
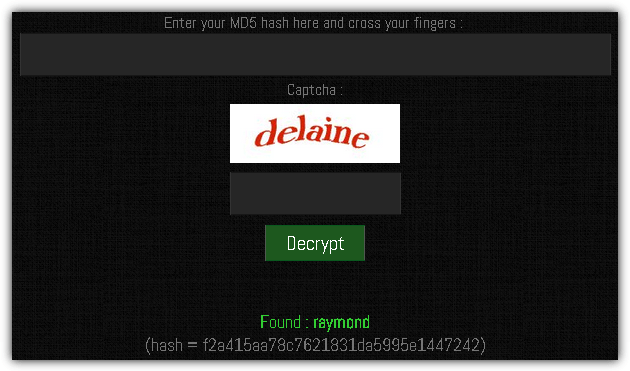
Unlike most of the online websites that have their own database of MD5 and words, md5crack.com uses a combination of search engine indexes and rainbow tables to help search for a word matching the given MD5 hash. Free API usage without limitations is also available to everyone although the usage is closely monitored to prevent excessive use.
3. md5cracker.org
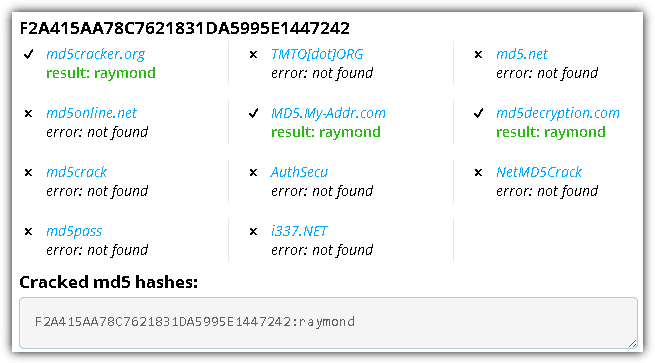
md5cracker.org shows that it automatically searches 11 different websites for a matching word of a provided MD5 hash. However after manually testing each database, we found that half of them don’t work anymore. It is still useful because the results are shown in real time without the need to refresh the webpage.
4. md5decrypt.org
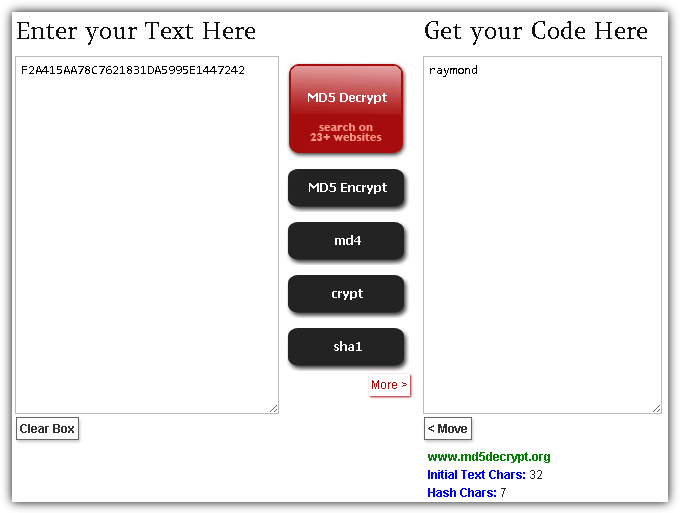
Similar to md5cracker.org above, md5decrypt.org claims to search your hash on over 23 other websites for a matching word. It is hard to tell whether md5decrypt.org did crawl over 23 website to search for a matching word because it does not list the other websites being used and the search is very quick, that always takes nearly the same amount of time to return a result.
5. crackstation.net
crackstation.net is a password hash cracker that can automatically recognize different types of hash functions other than MD5 and search for the correct password for the given hash. It is able to accept up to 10 hashes at a time and uses their own wordlist consisting of every word found in Wikipedia and every password list that they could find. Other than that, they’ve also made their wordlist more efficient by applying intelligent word mangling.
6. hashkiller.co.uk
Hashkiller.co.uk has been around since 2007 and has decrypted over a whopping 43 billion MD5 hashes to date! The decryption form accepts up to a maximum of 64 MD5 hashes to check at a time. They have a public forum which is very helpful because anyone can sign up for a free account and post a hash cracking request as long as it is below 25 hashes.
7. reverse-hash-lookup.online-domain-tools.com
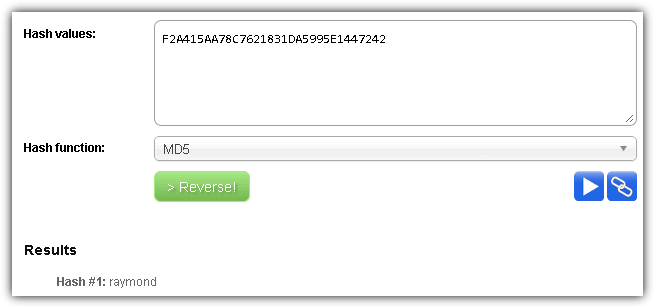
Online Domain Tools is a website that provides many useful tools that can be used for networking, domain, web, browser, security, privacy, data, conversion, and coding purposes. One of their tools is a reverse hash lookup that can decrypt MD5, SHA1, SHA-256, LM and NTLM hash function to plaintext message. The form allows up to 5 hash values at a time and the result is shown instantly at the bottom of the form. The lookup is based on several online databases as well as engines using rainbow tables.
Visit reverse-hash-lookup.online-domain-tools.com
8. md5decrypt.net
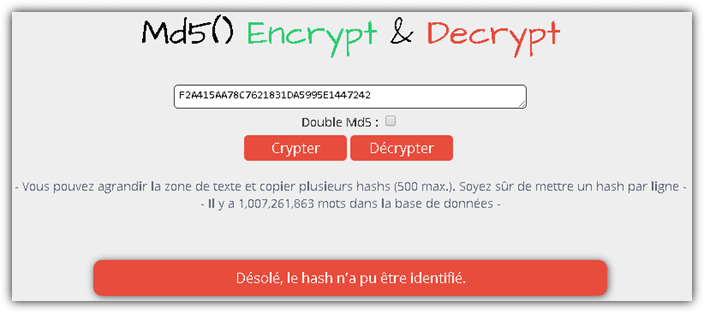
md5decrypt.net’s database contains over a billion words but still is not considered to have one of the biggest wordlists. However, what we like about md5decrypt.net is the clean design with no advertisements at all and the ability to search for words that are hashed twice. A useful tip is the text box can actually support multiple hashes up to a maximum of 500 by putting each hash in a new line.
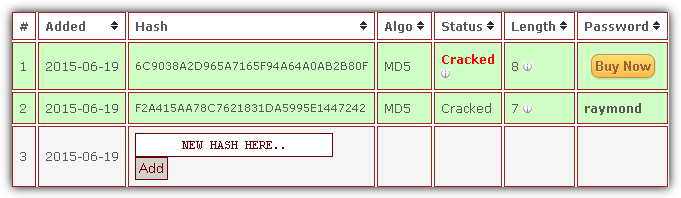
9. onlinehashcrack.com
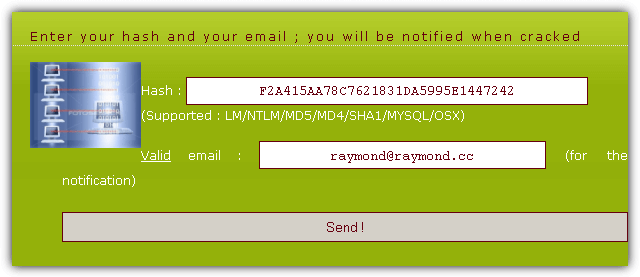
onlinehashcrack.com is a slightly more professional service to crack your hash. A few techniques such as Rainbow, Hybrid, Wordlists, and Bruteforce are being used to crack a hash. Any cracked hash containing 8 or more characters will require a payment of 3€ to reveal the password while anything below 8 characters is free. You will need to enter a valid email address to receive a notification when the cracking process has been completed and to access a private URL containing the result.
Apart from cracking MD5 hashes, they can also crack WPA/WPA2 in *.cap or *.pcap file extension. A useful hash identification service is useful to determine the type of hash being used.
10. cmd5.org
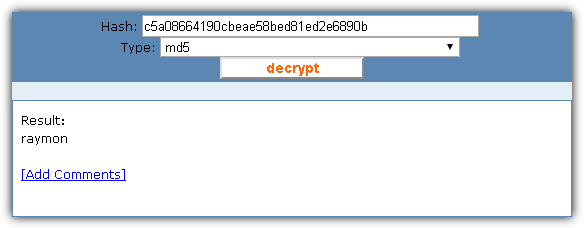
cmd5.org claims to have the largest database in the world with 7.8 trillion unique records. They are similar to onlinehashcrack.com whereby they offer both a free and paid hash cracking service. Although not mentioned anywhere on their website, it seems like a cracked hash containing 6 characters or less is free while strings containing 7 characters or more require payment. Their cheapest package is they accept a minimum payment of $20 that includes 1000 hashes with no expiration to the credits. This is the only one that managed to decrypt the MD5 of the word “raymond.cc”.




User forum
0 messages