Detect and Remove DarkComet RAT Malware used by Syrian Government
DarkComet is a remote administration tool that opens an invisible backdoor giving the controller full access to the computer including access to the hard drive, activating webcam and sound capture, keylogging to steal username and passwords by capturing keystrokes and many more. DarkComet is one of the very few free remote administration tool that has been in development for such a long time. About 2 months ago CNN reported that the Syrian government was using a free and publicly available remote administration tool called DarkComet to spy on the supporters of the Syrian opposition. When the coder of DarkComet got to know about this, he quickly created a remover for his own tool to fix what the Syrian government did to the opposition movement.
Since DarkComet can be downloaded publicly, the server file that is generated from it is obviously fully detected by most if not all antiviruses. So anyone with the intention of infecting another person’s Windows computer will have to make the server file fully undetectable by crypting it to bypas the antivirus detection. What makes DarkComet RAT Remover special is the ability to detect DarkComet’s presence even if it is virtualized, packed, encrypted, compressed or obfuscated.
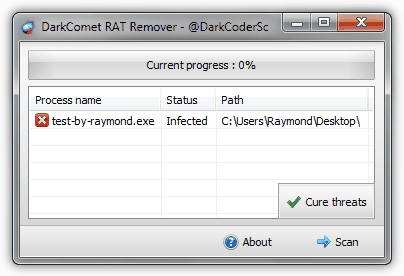
DarkComet RAT Remover is a portable and simple to use tool that is able to detect DarkComet RAT instance by taking a few minutes to scan the memory and offers to cure the threat in just a click of a button. The DarkComet removal tool also shows the process name and the installed location if the presence is found. Since modern Windows operating system such as Windows and 7 has UAC enabled by default which protects third party application from modifying the registry, it is advisable to run the DarkComet RAT Remover as administrator by right clicking on the tool and select “Run as administrator”.
As you can see from the video demo above, the DarkComet RAT Remover is able to detect the presence of DarkComet but the ability to remove the infection is a bit weak. DarkComet RAT Remover terminates the process but the file and registry entry that makes it auto start with Windows is still intact which means that when Windows is restarted, DarkComet will run again. The persistence installation option at the Module Startup is not even enabled during the creation of a new stub.
Another powerful option found in DarkComeT RAT that definitely breaks the DarkComet RAT Remover tool is the persistent process option in the Module Shield. When this option is enabled, the server process will automatically restart when it is killed or terminated.
Perhaps the DarkComet RAT Remover is very useful to detect its presence but shouldn’t fully rely on it to remove the infection until the cleaning function has been polished. The latest version of DarkComet RAT Remover was released about 2 months ago and this file has been constantly being scanned in VirusTotal with the result of a perfect zero (0/42) detection. Rest assured that the DarkComet removal tool is definitely safe without any backdoor being embedded to it that is if you download from the official link below.
now if we can only hear more about Detecting and Removing Malware used by u.s. Government
Has this been tested on known to be clean Pc’s? testing for false positives? So far the only Pc’s that did not have the infection was because the tool was not run in admin mode.When run in admin mode all have come up with the security center disabler infection.Even fresh clean installs. So has the tool been tested with clean machines?
@mowrrrman I think that if disabling the security center was the reason making the tool, it would not say it loud : security center blabla, it would just have said DarkComet Rat found, or maybe disable it in the background and not say anything, so Thanks Raymond anyway :) .. that’s my opinion..
and thanks again for all the people who tested and shared their experiences :)
Lol!!! I tried this on two PCs in one Laptop. Detected infections which I fixed or at least I thought. After rebooting the security center was broken in all three machines. Ran system restore and now everything is fine…
@mowrrrman: This is the programming error made by the author of this tool and it’s not bogus. It is able to find the malware process if exist in memory but the additional registry check on this tool is unnecessary. Although I would say that it is unfair for you not to vote just because I shared this, it’s still your decision and I can’t force you to vote, can I?
I am convinced that this is a completely bogus tool. I believe that it will find the rat on every pc tested…. I believe the only reason it was made was to turn off the windows security……I am surprised and sad. No vote for you.
@Freewear The infection was called “Security center disabler” and after pressing ‘Cure it’ I have to manually start the security center after every re-boot. And when I ran DarkcometRAT remover it said my system was clean . But I went to ‘Services’ in the control panel and set Security center to Automatic start on windows startup . Now if I scan with DarkComet RAT remover it sad Infected . The infection was called “Security center disabler” and after pressing ‘Cure it’ I have to manually start the security center after every re-boot AGAIN !!!!!!! So I concluded this is a false positive or probably my security center is infected “SOMEHOW I dont know ” and i dont know how to fix it .
I checked both infected machines after the “supposed safe mode clean” and discovered both xp and win7 64 had the security center shut off. Anybody know if it was shut off before the “clean” or if it was after the “clean”……. I do have one more Pc here that came up as infected that I have not cleaned yet. If it is still on before the cleaning I will have to vote this tool as bogus. Guess I will answer my own question…. Ok it was off. I am still wondering if it was off before my first failed attempts at cleaning or if the dcrt was what shut it off in the first place. Maybe the best way to find out if you are infected is to check the security center first before running the Tool? or is the real purposeof the tool to shut off the security center? Did anybody check the security center setting before running the tool? I do have more Pc’s here so again I will answer my own question. I’ll get back with the answer.
looks like running in safe mode worked for me too! with 7 Pc’s in the house all infected somehow??? This was a God send!!!! Wish I could find how this happened? hope ya win!
Thank you Laptop for your update, I really appreciate your effort :). On Win7 64x I noticed the same thing, Security Center Service is turned off also :)
UPDATE on XP3 SP3, If you get a Infection Report “security center disabler
” – infected! and you select “cure threat”, the tool switches off the Windows XP Security Centre service. To fix I have retarted the service and changed the blank Startup Type field to “Automatic”.
I have same Query as “Mcphlen” I have only tested on three XP machines and All of them I get Positive: – Process name : “Security Center Disabler” and blank “path”. So I was wondering is this something a genuine antivirus has to do to windows to stop false-alerts from windows when the Kaspersky/Norton has taken over protection?
after running as admin I too was told I was infected. Then I checked pc’s that have not been run in months and they were infected also. So I wiped my hard drive and reinstalled win7 64. After I got all the updates and a minimum of software including antivirus and a firewall,,,, I tested again and still was infected. So i am suspecting this tool is bogus. If it is real how can it be removed manually as this removal tool doesn’t work at all except to give a false positive I am suspecting…
Btw i scanned my system several times with the removal tool and the dark comet kept coming back with each reboot, until i disinfected it in safe mode and now it says that my system is clean.
Seen the malwarescan tool called D7?
sites.google.com/a/obxcompguy.com/foolish-it/d7
I say it’s, “An Absolutely.Amazing, shell scripting, clean your system, tool.”
How can i remove dark comet manually?
@Chiku – What infection did the removal tool say you had?
I ran the tool and it found nothing but I ran it as administrator and it said “security center disabler
” – infected!
Apparently, several posters here experienced the same thing:
malwaretips.com/Thread-Darkcomet-Remover-Tool
Raymond – did you run the tool as administrator? Here’s my forum post:
raymond.cc/forum/spyware-viruses/33219-dark-comet-remover-tool-security-center-disabled-infection.html
imgur.com/uQXdJ
@Chiku: A privately crypted trojan can definitely bypass detection by any antivirus or antimalware software. If an antivirus says that your computer is clean, you should not trust that 100%.
OMG …….my comp was infected I have almost scanned my comp with 5 antivirus and anti malware program including norton and malwarebytes and this program found it. Thumbs up to you raymond !!! hope there is no more hidden malware that can only be detected by the software made by the developer in my comp.
@Dr. Sheldon Cooper, Phd: The author’s website has link to download DarkComet which is known as a backdoor for some antivirus software. Linking to a bad neighborhood can be a bad effect to my blog. So I dare not take the risk. The download link at brothersoft is uploaded by the author himself. So it’s the same.
@sjf: Glad that the removal tool found and removed DarkComet backdoor from your computer. Someone has been monitoring and controlling your computer. Make sure you change all your password to be safe.
Raymond, why did you link to Brothersoft rather than to the removal tool link located on the author’s site?
I used the remover and was surprised to discover DarkComet RAT present in a process. After removal, I restarted the system and ran the scan again to see if it would come back. It didn’t. I restarted/scanned two more times, but DarkComet didn’t return. It worked for me just as the website indicated. Very pleased about this find! Even if I had to remove it manually, it was worth knowing.
Might be good IF you could actually FIND the download link among the dozen or so of adware links and other software download links on a questionable Brothersoft page.
Raymond, Could you fix the vertical toolbar position? It is on top of the first 2 paragraphs… I’ve seen it on 3 different position, and a couple of days ago, the position was excelent as it wasn’t on top of any article’s info/data.
Many thanks for your (and the others writers, of course) reviews and all the best for all of you.
Thank you Raymond, and thanks for the developer of the tool,
nevertheless, I noticed that everytime I scan as administrator, I get that my computer is infected :
Process name : Security Center Disabler
Path : “empty”
I tried to check on the internet about it trying to find out what file should I be concerned about, all that I could find was people saying that it might be a “bug”..
just wanted to share my experience. thanks again!
@sjf: There are many software that claims to do this and that, but yet most of the time they don’t.
To be fair, it is also possible that I may be testing it wrongly which is why I’ve embedded a video demonstration as a proof.
According to the DarkComet website located here:
darkcomet-rat.com/dcremover.dc
“If detected it will uninstall the program and also clean the registry alteration and keylogger logs.”
Thank you!!! I have Quick Heal (updated), yet it fails to detect the malware…. Thanks again to help!!! :)
this why i moved to cybergate ages ago