How to Customize U3 USB Smart Drive to Become Ultimate Hack Tool
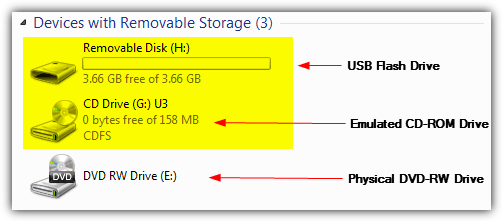
Have you ever wondered if it is possible to automatically and silently hack into a computer to steal important data or plant a backdoor by just inserting a USB flash drive? It was possible on Windows XP computers by using a U3 smart drive due to the weak built-in security on the operating system. A U3 smart drive by SanDisk or Memorex looks exactly the same like any other normal USB flash drive except it comes with an additional emulated read-only CD-ROM partition along with the removable storage disk drive. Plugging in a U3 smart drive will show up 2 drive letters in Computer rather than just 1.
The original purpose for a U3 to have an emulated CD-ROM on a USB flash drive is to automatically run applications such as the U3 Launchpad which is similar to the Windows start menu when the U3 smart drive is inserted to a computer using the Windows AutoRun feature. This is similar to inserting a software installation disc to a computer and an installer menu will automatically appear. To turn your U3 USB smart drive into an ultimate hack tool, all you need to do is modify the content on the emulated CD-ROM such as the autorun.inf to instruct Windows to automatically run your payload instead of the U3 Launchpad when the drive is connected to a computer.
One of the most popular and easy to use payload is called USB SwitchBlade. The package comes with a universal customizer tool that writes a custom ISO image file to the U3 partition and the payload that is copied to the storage drive can be configured by running the application and check the appropriate boxes. Here are the steps to install USB SwitchBlade payload to a U3 smart drive.1. Plug in your U3 smart drive to your computer.
2. Download Universal U3 CD-ROM Customizer (Universal_Customizer.exe) and extract to a new folder.
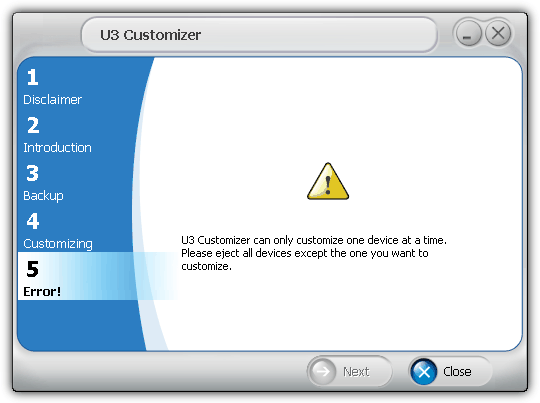
3. Run Universal_Customizer.exe as admin (Right click > Run as Administrator). If you received an error message like the one shown below, you are probably using an older version 1.0.0.8 that only works on XP. Make sure you download the Universal Customizer version 1.0.5.5 from the link provided by us.
U3 Customizer can only customize one device at a time. Please eject all devices except the one you want to customize.
4. Select Accept and click Next.
5. Click Next again.
6. Change the location of the backup if you need to and specify a password to protect the backup file.
7. Click Next and the updater tool will start backing up your files from your U3 smart drive and then write the USB SwitchBlade payload to the emulated CD-ROM drive.
8. Download -=GonZor=- Payload Config tool and extract the files from archive to the storage drive of the U3 smart drive.
9. Run SBConfig-V2.1.5.exe from the storage drive and check the boxes that you want the payload to be active. For example, checking the “Dump Firefox Passwords” option will attempt to extract all the passwords saved in Firefox and save it to the storage drive.
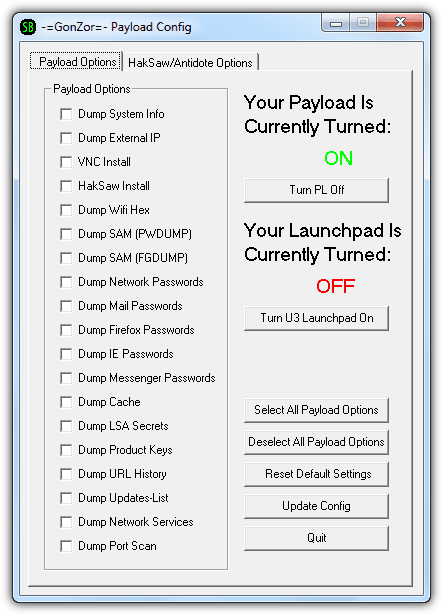
10. Click the Update Config button once you’ve completed selecting the payload options.
Your ultimate USB hack tool is now ready. Simply plug in the U3 smart drive to an unpatched Windows XP computer and it will automatically run the payload invisibly to extract and save the information to the storage drive on your U3 smart drive. The whole process should take about 30 seconds to a minute to complete depending on the speed of the computer and also the amount of data to dump.
Page 2 contains instructions on how to update the tools within the payload and also important information about this technology.
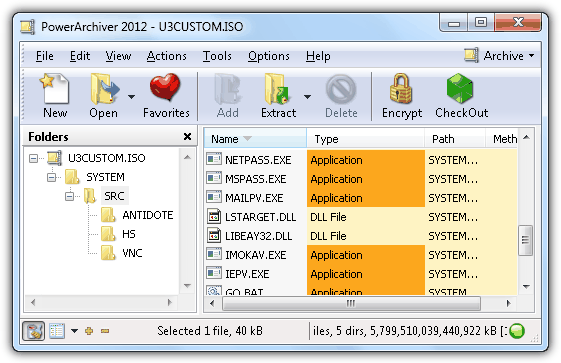
Most of the existing tools within the SwitchBlade payload are dated few years back and may not work efficiently on the newer targeted applications or Windows operating system. To update the tools, simply mount the 12.5MB U3CUSTOM.iso from the bin folder or open it with an archiver software. Download the latest version of ProduKey, Protected Storage PassView, Network Password Recovery, MessenPass, Mail PassView, IE PassView from NirSoft and FirePassword from SecurityXploded and replace the old version in the U3CUSTOM.ISO with the latest versions.
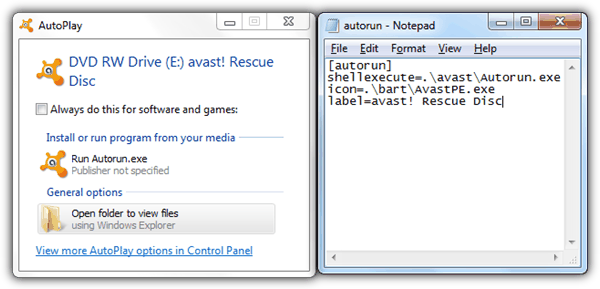
Important Note: On 2009, Microsoft has made a decision to turn off the AutoRun feature because it accounted for a large percentage of malware infections. Here is an example of avast! Rescue Disc that contains an autorun.inf instructing Windows to automatically launch the Autorun.exe from the disc but in Windows 7, the AutoPlay dialog box shows up instead.
Not long after the announcement by Microsoft, SanDisk too announced that they will phase out U3 smart drives since U3 highly depend on the Windows AutoRun feature to work. Although you can still find a few sellers selling the U3 smart drives on eBay, it is nearly impossible to run the payloads silently and automatically due to the disabled AutoRun, UAC restrictions and the possible antivirus software installed on the target computer that is able to block most if not all of the popular password recovery tools such as the ones by NirSoft found in USB Switchblade.
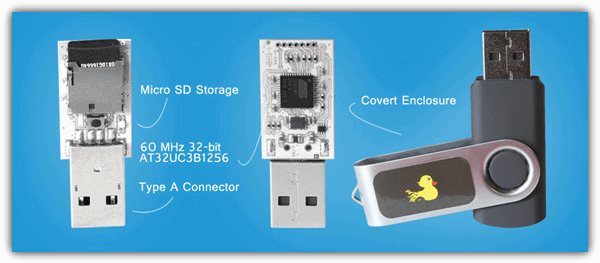
Since USB Switchblade no longer works as it should on newer Windows operating systems, the Hak5 team has designed a new kind of attack that works on Windows, Mac and Linux through HID injection and is called USB Rubber Ducky.
If you own a U3 smart drive, it can be still useful in the sense that you can store important data to the emulated CD-ROM drive to prevent the files from being accidentally deleted or corrupted by virus because USB flash drives with read-only or write protect switch are getting rare nowadays.
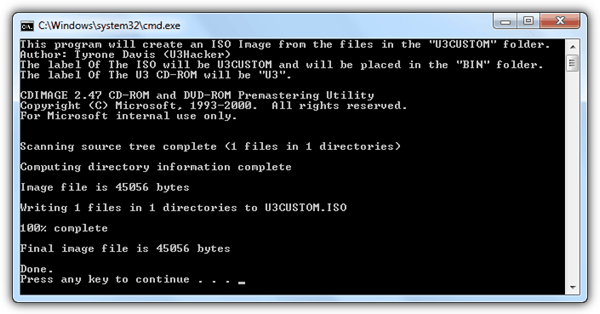
If you want to write your own files into the emulated CD-ROM drive, simply copy the files to U3CUSTOM folder from the Universal Customizer and run ISOCreate.cmd which will automatically create a U3CUSTOM.ISO file to the bin folder. Then run Universal_Customizer.exe and follow the instructions to burn the U3CUSTOM.ISO to your U3 smart drive along with your files.
If for some reason you want to uninstall the USB SwitchBlade and restore back the SanDisk U3 Launchpad onto your U3 smart drive, simply download LPInstaller.exe from the official SanDisk website and run it.
If you find the emulated CD-DRIVE useless and want to fully uninstall it since there is no support for the U3 Launchpad and all U3 application download servers have been taken offline, download the launchpadremoval.exe tool from SanDisk and run it. The U3 partition will be removed and the U3 drive space will be merged to the storage drive.
Does this still work in windows 7 and higher or has this been blocked?
Cool this actually worked. Tested it in a vm found some old SanDisk u3 uses lying around I use this a lot back in the day. Worked on windows 10
served in windows 7 and 8 ?
what the password please…
for
Universal_Customizer_1.4.0.2.zip
GonZors_SwitchBlade-V2.1B.zip
Password is listed on the download page…
where?
On the download page…
thanks.
really awesome hack
Hello
I have tested it..it’s very cool.
wow..
I managed to combine the Amish Payload, ipod switchblade, and Silvernions Technique. It ROCKS, buts it takes about 45-50 seconds for it finish….. (hey there are downsides to all acts of brilliant hacking)
This worked great on my workgroup at home.
thanks man it worked. Thanks a lot!!!!
thanks for sharing this cool news. now i am also going to try some hack. thanks a lot.
Lol, I must admit that this is a good hack. Though the people asking for software are annoying. You shouldn’t be allowed to use this method if you can’t write your own payload software. By the way, half the the things that the payload does are blocked by a decent firewall. Like Comodo. It warns of things like silent processes and that.
thanks for the info
nice post by the way
Hehe.. good tips :)
Hey Raymond, You rock man!!!… i had a u3 device from long time but didn’t knew that it can be used for such purposes also… this is better then a keylogger which is detected somehow.. but no chance for this tool get caught.
Thanks a lot….