4 Ways to Edit Windows Registry Offline [Without Regedit]
Many years ago when I was still a novice in computers, I accidentally disabled userinit.exe from startup thinking that it was spyware using the SysInternals tool Autoruns. When I restarted the computer, I was unable to login to Windows. Whenever I select the user from the list, it logged in and automatic logged off. I had a really tough time trying to restore userinit.exe back to the Windows startup list as it wasn’t easy accessing and editing the registry when Windows is unbootable. Autoruns is much smarter now because when you uncheck userinit.exe from Logon, it will warn you that “disabling or deleting Userinit will prevent users from logging on”.
In the end I managed to fix the problem but couldn’t exactly remember how I did it because I tried many many ways and I got lucky. I eventually found a real solution on how to edit Windows registry key values without booting into Windows. This is also useful for editing malicious startup items such as rogueware and ransomware. If you have a similar situation as my previous case which requires you to edit the registry without Windows, then here is how to do it.
Listed here are 4 methods to edit the Windows registry keys using a bootable CD. Although you are being shown how to repair the userinit registry key, these methods can obviously be used for any other keys in the registry that need to be edited.
Method One
This first method uses a great free tool called PC Regedit which lets you create, delete and edit Windows registry key values without Windows.
2. Burn the downloaded PCRegedit.iso to a CD. Refer to this guide on how to burn ISO images on a CD.
3. Boot up the computer with the PC Regedit disc and it will load up ISOLINUX.
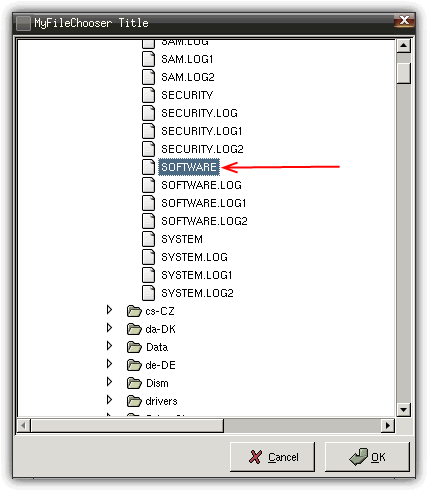
4. When everything is loaded, you will see a MyFileChooser Title window. By default you are at the Config folder. Scroll down a little, select SOFTWARE and click OK.
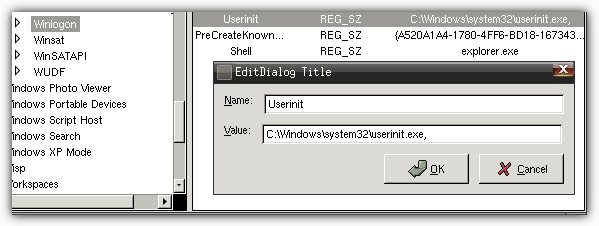
5. Navigate to Root -> Microsoft -> Windows NT -> CurrentVersion -> Winlogon.
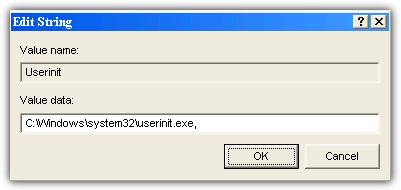
6. Look for the Userinit key and make sure that the value is set as:
C:\Windows\System32\Userinit.exe, (including the comma)
If the Userinit key is not there, you can add a new key by right clicking at the right pane and select Add Key.
You can use this method to load up other registry files and edit them. Here are the explanation of the 5 registry files for HKEY_LOCAL_MACHINE.
Registry Location: HKEY_LOCAL_MACHINE\SOFTWARE
File: SOFTWARE
Backup: SOFTWARE.LOG
Registry Location: HKEY_LOCAL_MACHINE\SECURITY
File: SECURITY
Backup: SECURITY.LOG
Registry Location: HKEY_LOCAL_MACHINE\SYSTEM
File: SYSTEM
Backup: SYSTEM.LOG
Registry Location: HKEY_LOCAL_MACHINE\SAM
File: SAM
Backup: SAM.LOG
Registry Location: HKEY_CURRENT_USER
File: NTUSER.DAT
Backup: ntuser.dat.LOG
Registry Location: HKEY_USERS\.DEFAULT
File: DEFAULT
Backup: DEFAULT.LOG
On Windows-NT based systems such as Windows NT, 2000, XP, Vista and 7, each user’s settings are stored in their own files called NTUSER.DAT and USRCLASS.DAT inside their own Documents and Settings subfolder (or their own Users subfolder in Windows Vista or 7).
Method Two
This method involves using the popular Hiren’s Boot CD and its Mini Windows XP feature to edit the registry.
1. Download the Hiren’s Boot CD ISO.
2. Burn the downloaded Hirensbootcd.iso to a disc. Refer to this guide on how to burn ISO images on a CD.
3. Boot up the computer with the Hiren disc and and at the menu select “Mini Windows XP”.
4. When the Mini XP is loaded, click the Hiren menu icon in the tray -> Registry -> Registry Editor PE.
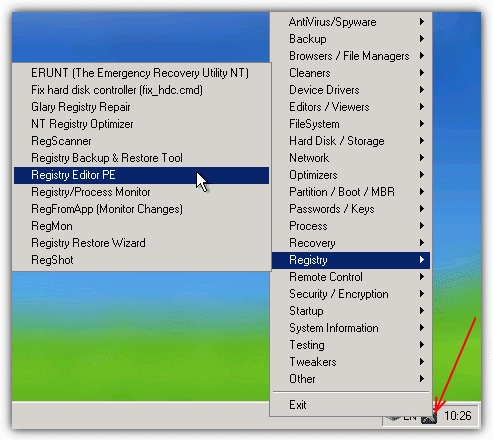
5. When asked to, set the remote Windows directory (usually C:\Windows) and press OK.
6. Click OK on each window to select the related registry hive. If you want to edit a registry value from HKEY_CURRENT_USER you will need to select Yes when asked if you want to load an NTUSER.DAT and locate the file in the user directory.
7. Expand HKEY_LOCAL_MACHINE and the hives will automatically load with the _REMOTE_ prefix. Navigate to _REMOTE_SOFTWARE -> Microsoft -> Windows NT -> CurrentVersion -> Winlogon
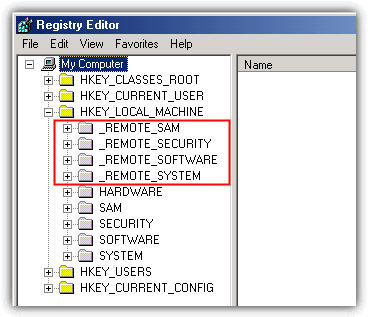
8. Double-click Userinit and set it’s value to “C:\Windows\System32\Userinit.exe,”. Make sure you include the comma at the end after Userinit.exe, it is there by default.
8. Close the registry editor and the hives will be automatically unloaded.
The 3rd and 4th method can be found on page 2.

Alain guy is right , add 5th method f8 –> windows repair—> cmd —> regedit…….
Ultimately i am create registry & working correctly..Thank you Sir!
Thanks, a very useful post!!!, I didn’t know I was that easy!.
Another way is Linux and “chntpw” to edit the Windows registry.
What can I save, when you Rock, Raymond, you ROCK
You are my life saver Mr. Raymond. I used this method through A virus rescue system & BANG….. It rocks man..
Thanks, this post save me
Pcregedit site is dead
Try “Registry Editor PE”
U are the best Raymond
Really Really … can’t thank u enough
with my all wishes to u to achieve your wishes in your life
u can’t imagine how u help me through these .. u are a real genius
thank u , and … stay blessed :)
It worked for me. Revived an old XP desktop after sitting for 4 years. I had the logon logoff loop, possibly made worse by Nortons 360 as I could not run in safe mode.
1) Used FixMeStick to remove viruses;
2) Used Method 1 PC Regedit.iso to enter missing userinit as described above;
3) Used active@LSoftTechnologies to burn above ISO to CD.
Raymond, there is a 5th method which does not require any tools/booting on an external CD if you have access to the repair utility
See explanation here
mattterrabyte.wordpress.com/2011/07/17/modify-windows-registry-startup-repair/
I think you should add it to your list
Thanks for the solution , was trying to delete a record that did not exclude .
.) Start on Windows install CD
.) At the “Install Now” selection screen, hit Shift+F10 to open a cmd box
.) type: regedit (or regedt32) then Enter
Moreover:
.) Click on HKLM (for instance)
.) File/Load Hive, find your hard drive letter (ex: D:), load D:\Windows\System32\Config\SYSTEM and give hive a name (ex: DEBUG)
.) Do any modifications you want within this hive
.) When done, select the hive (DEBUG) then File/Unload Hive
Hi, thanks for the info & Hirens Boot CD download link – looks like a useful tool !
Thank you so much!! you are a life saver!! i just built my first pc ever and thought of tinkering the registry, which is sstupid stupid stupid on my part. heartbreaking to not getting it working after that. but after i went to do your methods i got it back up! thank you so much!!
THANKS MAN YOU’RE VERY HELPFUL THAN OTHER WEBSITE OR BLOG I’VE FOUND ON HOW TO BOOT/REPAIR USING USB FLASH DRIVE AND SO FAR YOUR BLOG HELP ME SO MUCH. THANK YOU! :)
thanks a lot man.. awesome tutorial
Thank you so much for this! I corrupted my registry by following vague registry edit instructions, and the first method here got me back in business.
Note to other users, I had to do a Binary Edit. Simply Editing the values was not suffcient.
Cheers!
Thanks a lot
Thanks a lot!!!
Awesome, thanks!
thank you so much
I had a problem was with the RPCSS not starting correctly on my laptop, this tool made it easy to rectify! Whoever made this is a genius.
A thousand thanks for the tutorial, I have use PCREGEDIT several times and it is great.
This post just saved my life. OK, maybe not my life, but a hell-of-a lot of trouble. Thanks!
A thousand thanks for that, it saved my tail today.
you are so good, I like you!
PC Regedit saved me big time! THanks Raymond!
hi
thank soooooooooooo much
it was great
i suddenly deleted “userinit” key patch in registry and i couldn’t do anything
i used hirens boot CD (mini windows xp) and edited my registry in the way you said
again thanks so much
Thank you and Thank you again Raymond for this detailed explanation on how to use PCregedit to restore userinit; I have regain control of my pc after 5 hours of pure panic! Thanks also to the PCregedit team, wherever they are.
This is an awesome page compared to dozens I have been through today.
All the best!
This really worked for me. I used Bart PE to access the registry edit. I have spent days over the last few weeks trying to solve this problem and this finally did it. It was due to a virus either w32silly – forever.exe or music.exe which came onto the computer via an infected USB memory stick. I was aware that the userinit.exe file was the problem but the other solutions suggested elsewhere never worked (perhaps it was the comma at the end?) Thanks very much.
Thanks a million Raymond, you’ve saved me a LOAD of work with this tutorial! Awesome work and highly appreciated. Highly!!
You are a genius!!! Thank u so much!!
Login Logoff Loop no more. What a great post, easy to follow Deliastyle walkthrough. Thank you.
Many thanks Raymond – this link was a great find. I have never seen this problem before & I have been working in IT for many years. I tried numerous things but continued to scratch my head for two weeks before finding this article. It thankfully saved me from the time consuming PC rebuild, which I was beginning to think was my only option – well done for producing a great fix.
Many thanks to you and the author of PCRegedit, this saved me.
Nice to know have software like this.
Thanks for posting this. I have been working on computers for 9 yers. and this is the first time I saw the logon loop issue. My client and I thank you!
Thanks bro. Your tutorial has save my wifes laptop. I use PC Regedit and burn it into a cd. Then i follow your instruction. Thanks once again.
wow, that’s perfectly works! thank you so much!
Hello Raymond, I had a similar problem with you. The problem with my case is my useinit file was infected with a virus still can’t figure out yet. Realizing my userinit.exe file was infected (through virus scan), i simply disable the userinit entry in Autorun.exe (by sysinternals) and wasn’t too care about what the dialog box was talking about. Simply clicked Ok, then the next time i restarted my PC, the infinite logon-logoff loop strike me.
Through my other PC i manage to Google this page. Man, what you’ve done is what we as PC not-so-expert user commend. Thanks bro! You really saved millions others who are careless enough to mess with their useinit.exe entries in the registry. Hehehe.. Cheers..
Wow, thanks you saved my wifes laptop.
Thanks again!!!!!!!!!
Man,
You really saved my bacon with this fix – many, many thanks. There were two things that I had to do a bit differently, though (I used the PC Regedit fix for my situation).
1) Even though I couldn’t logon, Windows did attempt to start so I went into the BIOS setup to disable the A: drive and HDD, forcing the CD drive to be seen.
2) After navigating to the offending key, I had to edit the key instead of adding a key.
Other than that, your fix worked perfectly and, again, many thanks.
Erich Frerking
Thank you, very good work. I followed the second option downloding PCRegEdit.iso
It worked just fine.
Thanks! You just saved my computer! I had a virus and was a bit too zealous in cleaning it out, messed with something in Hijackthis, and got caught in an endless logon/logoff loop. NOTHING worked, and I was ready to do system restore and just start over. Then I landed on this page and, seriously, a few minutes later my computer was back in working order. You rock!
Hello. Thank you for your help and guidelines.
Raymond thanks for tutorial ;)
Thanks Ray. I once had the same problem a few weeks ago and it really bugged me till I got BartPE. It works too.
hmm good tutor thanks i like it
Thanks mate, wonderful tip and nicely written tutorial, cheers!
Hey Ray,
Another good tip. Thanks man, you are awesome.
nice tutorials thanks ray!
Thanks Raymond.
thanks for the wonderful tips.
Anyways thanks and cheers :)