4 Free Tools to Sandbox Programs and Keep Your Computer Safer

A sandbox simply means a way of running a program in an environment which separates it from the host operating system. There are several ways of sandboxing a program. One is to use virtual machine software like VirtualBox which runs programs in a virtual operating system. Another way is to temporarily virtualize your real operating system so any changes made to it are discarded after a reboot. You can also portablize programs to isolate any changes they make from the host system.
Another easy option is to sandbox a program on demand so only that program is isolated leaving the rest of your system unaffected. Then you can simply empty the sandbox when you are finished to flush the contents of it away. Apart from being isolated from any potential harm caused by the sandboxed software, it’s also an excellent try before you install option to keep your system clean from unwanted file and registry changes.
Here we list 4 free applications that can sandbox programs you want to isolate from your main operating system. Sadly, the popular Avast Free Antivirus used to have a dedicated sandbox option but it’s now only available in paid versions of the software. All the programs below were tested in Windows 7 and 10 64-bit.
1. Sandboxie
Sandboxie is the most popular and well known program of this type and is often used by advanced users for testing the behavior of software. Although Sandboxie is shareware it can be freely used after 30 days with a timed nag window on launch. Features disabled in the unregistered version include forced programs and folders, force browsers to run in the sandbox and also only one sandbox can be used at once.
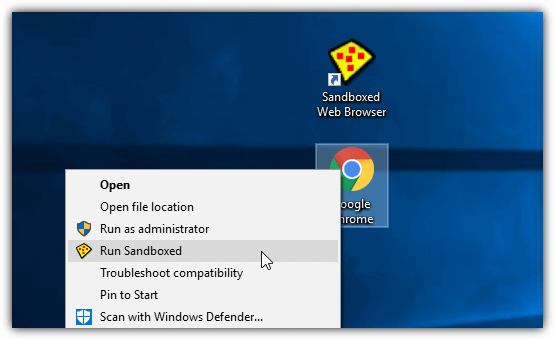
During install a “Sandboxed Web Browser” desktop shortcut is created which runs your default web browser in the sandbox. To run another program or shortcut, simply right click on it and select “Run Sandboxed” from the context menu (or “Send to” menu) or open the Sandboxie GUI and drop the program onto the window. The tray icon > DefaultBox menu has extra options to sandbox the default email client, sandbox Windows Explorer, browse for a program or open a custom mini Start Menu where you can select the program you want.
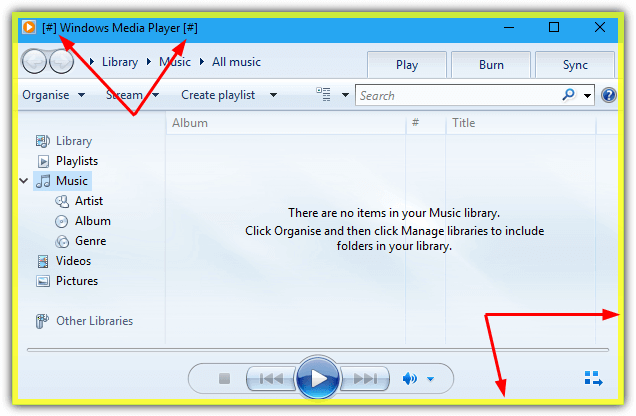
By default, Sandboxie puts a yellow border around the window of a program in the sandbox although you can change this to another color in the settings. If the window has a visible title, its text will also be encased in “[#]”. While programs you install inside the sandbox will stay until you clear the sandbox contents, the programs you run by drag and drop or context menu will not. They will need to be launched the same way every time as forced programs is a premium feature.
An option to run a program in Sandboxie automatically is to insert the following into the Target box of its shortcut before the path of the program:
"C:\Program Files\Sandboxie\Start.exe"
Therefore "C:\Program Files\Sandboxie\Start.exe" "C:\MyProgram.exe" would send MyProgram to the sandbox straight away.
Each different sandbox you create has a huge number of functions and features attached to it. These include quick and immediate recovery options to copy files from the sandbox, program groups, file migration into the sandbox, internet/network and start/run restrictions, resource access, enhanced compatibility for specific applications, and change the sandbox container folder. It’s also very easy to quickly kill running programs and delete or explore sandbox contents.
2. Cybergenic Shade Sandbox
What makes Shade an interesting alternative to Sandboxie is it’s easier to use. That comes at the expense of features and functionality though. An inconvenient part of the installation is Shade requires a free license key which is obtained by entering a valid email and any name during install. A temporary email service can be used if you prefer. After install and a reboot, open Shade and either leave it for a few seconds or press the button top left and press Activate to enter the key. Shade won’t work until you activate with a valid license key.
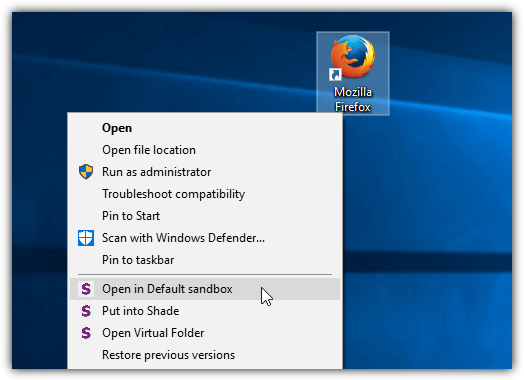
Programs can be isolated using Shade in a couple of ways. Firstly, you can right click an executable file or shortcut to show the context menu entries. They offer to run the program one time in the default sandbox, add the program to the sandbox or view the virtual folder. Alternatively, open the Shade interface, click the button and drop a program or shortcut onto the window. Click on a program in the window to launch it sandboxed.
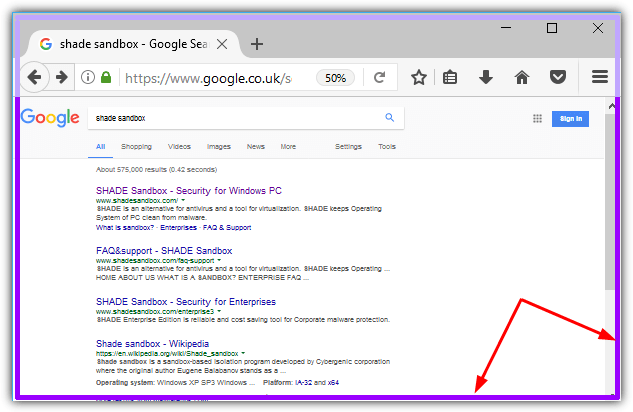
A purple border is added to the window of a sandboxed program. The border is not totally reliable though, and only partially appears or won’t appear at all with some non standard program windows. If the program has been added to the sandbox and its icon appears in the window, it will always automatically run sandboxed. Right click on the program/shortcut and select “Remove an application from Shade” or remove it from the Shade window by selecting the icon and pressing the remove button.
Sandboxed files are stored in a C:\Shade\{random name} folder. The same folder opens in Explorer if you press the Open Virtual Folder button in the Shade GUI. All the files can be deleted when you’ve finished with them by pressing Clean up sandbox. Shade Sandbox doesn’t have the advanced features of Sandboxie but that perhaps makes it more suitable for casual or less advanced users.
3. Comodo Firewall / Antivirus / Internet Security
Comodo is a well known security company and it has several free security products. The firewall especially is very highly regarded. The Comodo sandboxing component which allows you to run a specific program in a virtual environment is available in the Firewall, standalone Antivirus, and Internet Security products.
We are not fans of all the junk and unwanted software Comodo asks to install or force installs along with the main security application. While changing your browser homepage, DNS service, sending cloud/anonymous statistics and setting Comodo Dragon as the default browser can be opted out of, Comodo Dragon and the Geek Buddy premium tech support addon are force installed. The only good thing is they can be manually uninstalled later on.
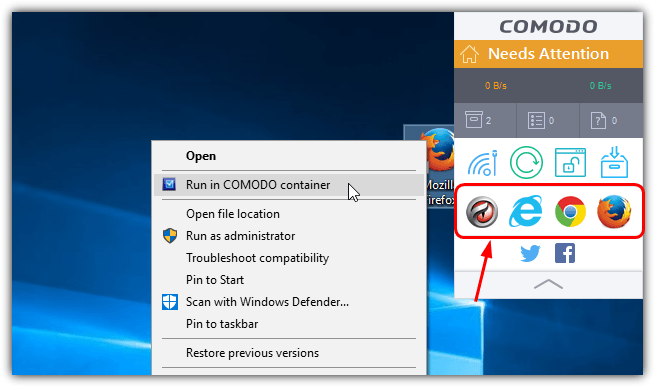
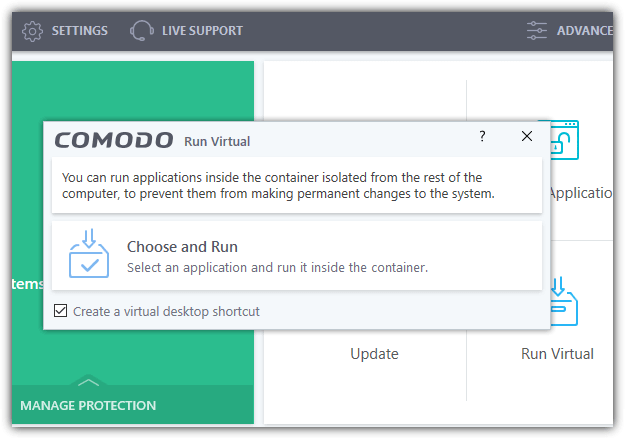
By default, Comodo adds a widget to the desktop which includes shortcuts to your installed web browsers. Click on a shortcut to start the browser sandboxed. Alternatively, you can right click on a shortcut or executable file and select “Run in Comodo container”, click on the widget Run Virtual button to run another program sandboxed or use the Run Virtual button in the main user interface. The run virtual option lets you browse manually for a file and also create a desktop shortcut.
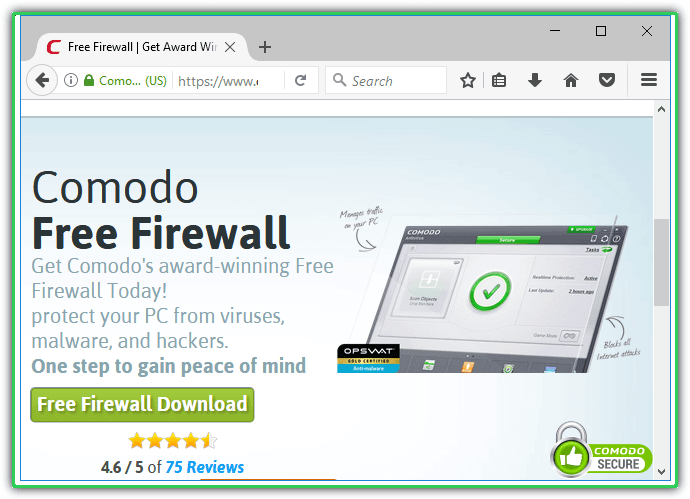
The border placed around a sandboxed program by Comodo is green. In Settings > Containment there are more advanced options to exclude files, folders, and registry keys/values, and auto start contained services. The Auto Containment feature can be used to sandbox specific programs automatically according to a predefined set of rules. The option to reset the container and delete all its files can be found in Tasks > Containment Tasks.
Download Comodo Firewall | Comodo Antivirus | Comodo Internet Security
4. Qihoo 360 Total Security (Essential)
Total Security is an antivirus from Chinese company Qihoo 360 that incorporates both Bitdefender and Avira antivirus engines. It comes in two free versions, the full version includes an application and Windows updater, WiFi security checker, junk file cleaner and a Windows tweaker/optimizer. If you don’t want all the extras then download the Total Security Essential version which just has the antivirus. Both versions include the sandbox.
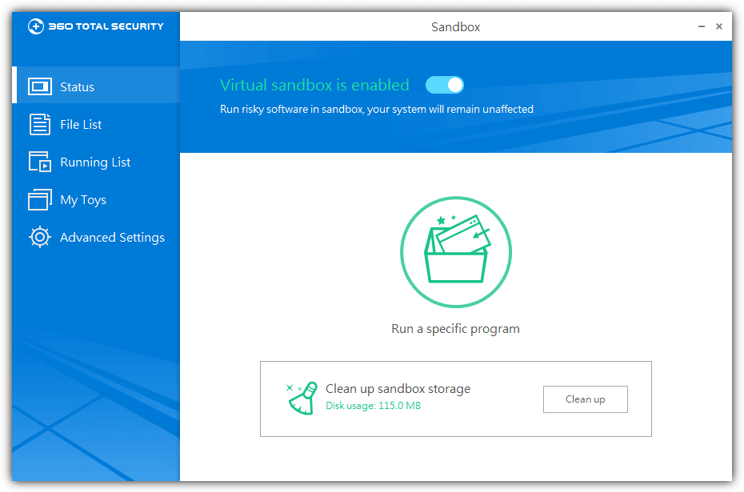
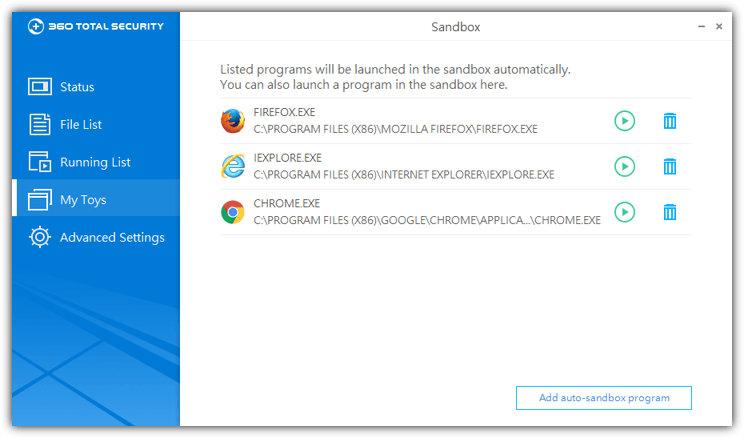
Running a program in the sandbox can be done a couple of ways. Either right click on the shortcut or program and select “Run in 360 Sandbox”, or open the main user interface, click on Sandbox and press the “Run a specific program” button to locate a file manually. You can also choose to auto sandbox a program every time it’s launched by going to the My Toys window and adding a program to the list.
Like the other software here, 360 Total Security adds a visual indicator to a sandboxed window, this one is a green menu and can be quite useful. There are small buttons to disconnect sandboxed programs from the network, open the manage sandboxed files window and auto hide the indicator. We’ve noticed the indicator doesn’t always appear though, minimizing and restoring the window will sometimes make it show up.
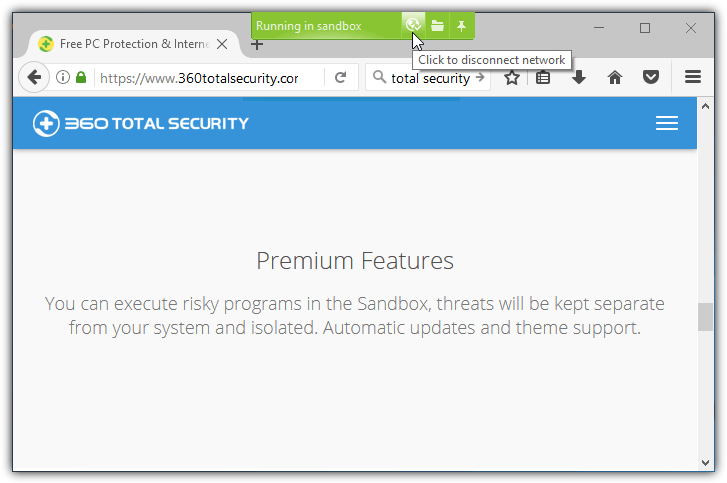
If the visual indicator doesn’t appear you can check in the Sandbox > Running List window to see if the program is sandboxed. Files inside the sandbox can be viewed in the File List window. They are split into media, documents or you can simply use directory browsing to delete or copy specific files. Use the Clean Up button to delete all contents immediately. Some Cleanup options like auto clean and exclude file types are available in Advanced Settings.
Download 360 Total Security | 360 Total Security Essential
Final Note: Although sandbox applications can successfully run several different types of program inside a sandbox, there are some that will not work. Software that installs its own services, software drivers or it requires high level access to the system will likely be problematic. For instance, most antivirus and security software or large applications that integrate into the system like iTunes or Visual Studio will have problems or not work at all.




User forum
0 messages