Recover Windows Login Password Online with LoginRecovery
There are many ways to login to a password protected Windows even if you do not know the password. You can reset the current password to a new password, make your Windows accept any passwords or decrypt the current password so you can login with the current password. Cracking the current password is the best method because it doesn’t reset and change the current password so no one would suspect anything. However this is also the most difficult method and can be very time consuming depending on the strength of the password. If the password is really long and contains uppercase, lowercase, numbers and symbols, it may take many years just to crack that password depending on the power of the machine that is used to run the decryption.
If you do not want to run the cracking tool on your computer for days/weeks/years in attempting to decrypt the user account password, you can do it at LoginRecovery where it provides an online service to help you decrypt the password just by uploading a XML file created by their LiveCD.
Basically the steps involves burning a LiveCD to a CD and boot up the computer. If an Internet connection is detected, the program will automatically upload the LM Hash or NT Hash and instantly start cracking. If there is no Internet connection on the computer, you can plug in a USB flash drive and a XML file will be automatically saved to the USB drive which can be uploaded to the LoginRecovery’s website from another computer. You can then check the cracking progress by entering your email address. It is that simple but we’ll still show you in details.1. Go to LoginRecovery’s website, enter your email address and click the Download Now button. It is important to enter your valid email address because you will need to use that email address to check the progress. You can also opt to download the ISO CD image so you can burn it with your favorite ISO burning software.
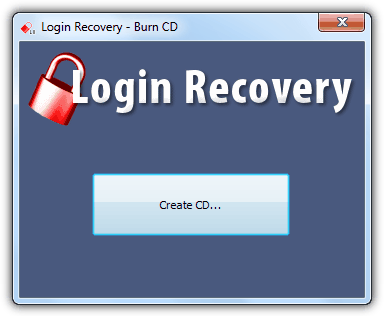
2. Run the downloaded Login-Recovery.exe file, insert a blank CD and click the Create CD button. If you inserted a used CD-RW, the program will prompt you to erase it.
3. Boot up the computer with the CD and you will see that the Login Recovery tries to locate the encrypted password.

4. Once the password has been located, it will then try to check for Internet connection so that it can upload the encrypted password to their server.
4a. If the upload is successful, you should see a message saying that “The passwords have been retrieved and the results have been sent to [email protected]”. Your computer will turn off automatically.
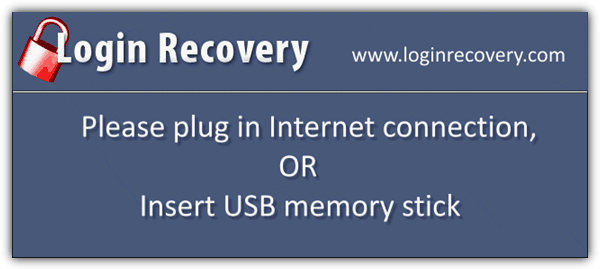
5. If Internet connection is not detected, the program will ask you to plug in Internet connection or insert a USB memory stick. If you want to insert a USB memory stick, make sure that it is formatted as FAT32 because the program fails to copy the password to a NTFS formatted pen drive.
6. Use another computer, plug in the USB drive and visit the Login Recovery’s upload page to upload the upload.xml file.
7. To check the decryption progress, go to the Results page and enter the email address that you’ve used in step 1.
From what we’ve tested, LoginRecovery managed to recover the following password raYmondcc, word168pass and even [email protected] on Windows XP. However Login Recovery seems to have a very low success rate on Windows 7. We tested 6 different passwords from Windows 7 in Login Recovery and only 1 common password “qwerty” was recovered while failed on “raYmondcc, raymondcc, raymond, splinter, word123p”.
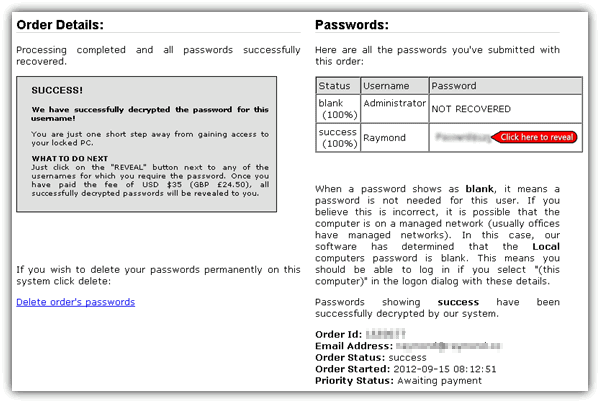
Login Recovery can probably recover all passwords from Windows XP, but definitely very limited for Windows Vista and 7. The catch for revealing the recovered password is to pay a service fee of $35 while passwords that cannot be recovered but can be reset cost $34.50. Login Recovery used to offer this service for free with a 48 hours of wait time before the recovered password is displayed but they’ve disables the free service. If you’re looking for a free solution, here is how you can reset the Windows user account password and here is how to use Ophcrack to decrypt the encrypted password using rainbow tables.


its amazing .
Thanks I love your post…
Thank you!
it is quite helpful.
I just found something about windows password reset methods.
It also support windows 7 password reset
Those all are free and very helpful!
Raymond, am impressed with your solution and research. keep it up.
this website is very educative