URL Sniffer Tools to Find Hidden URLs: Best to use in 2023
It’s becoming a growing trend these days that when you download a piece of software, you’re not actually getting the proper full setup installer. Instead you download a small front end executable that will download the real installer in the background when you launch it and proceed with an install. Although this method of supplying the software reduces the load on servers because you’re only downloading the full size installer when it’s required, it’s also frustrating because you need access to the internet when it comes to installation and not everybody has or wants web access all the time.
 Adobe Flash full installer downloads in the background
Adobe Flash full installer downloads in the background
Thankfully, most of the time the web installer is only downloading the full setup executable file that’s usually hidden away or not immediately obvious on the developer’s website. Although you can’t normally view the full path and direct link of the application URL when the computer is downloading files in the background, there are ways to get around this problem with the help of a small piece of software. This will allow you to download the full setup file and install it on any computer at a later date.
Packet sniffing tools capture the incoming and outgoing packets on your network and are able to view the data which will usually include the direct URL to other installer files, executable’s or even media files. There are many network tools around that can do this type of task like Wireshark or Fiddler, but they are more powerful and advanced. Here we list 5 free tools that can capture network packets and are very easy to use only really requiring a few mouse clicks to discover the hidden URL you’re looking for.
1. URLSnooperURLSnooper is a packet monitor tool that is able to directly sniff or snoop the full URL from a web installer or webpage. It uses the WinPcap capture driver for its sniffing tasks and you will need to install it manually from the folder if you’re using the portable version of URLSnooper. Here’s how to capture a URL:
Like all packet sniffing tools, it’s best to only start sniffing just before the file you’re trying to get the URL for is downloaded (or clear the history first), this way there is less data to trawl through to find what you’re after.
1. By default the program is setup to monitor only multimedia files and you need to go to the File menu -> Advanced and select “Show All” from the Protocol Filter drop down.
2. Click the Sniff Network button to start monitoring URLs on your computer and keep it running.
3. Run the web installer, program or click on the webpage link and let the main file download, or cancel after it’s started downloading. Go back to URLSnooper and click the Stop Search button.
4. Click the Protocol column to sort according to protocol type. Then look for a line with “GET exe file” (or “http exe file”) and you should see what looks like a link to an executable file. Double click to open it in your browser or right click and copy the URL to confirm it’s what you want. In the example below, the URL for the full 16MB Adobe Flash player installer is sniffed from the 2MB web installer.
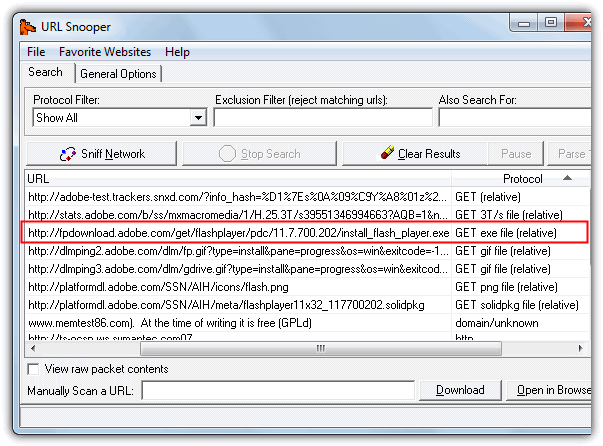
URLSnooper can also sniff out images and audio files etc, there’s specific mode to display multimedia links in the Protocol Filter.
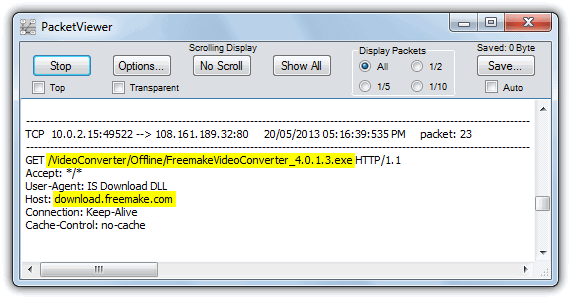
2. HTTPNetworkSniffer
HTTPNetworkSniffer is a tiny and portable utility made by Nir Sofer (Nirsoft) which captures HTTP requests and responses between your computer and the server and displays them in an easy to understand view. A good thing about this program is it doesn’t rely solely on the WinPcap capture driver like many other tools do. It also supports Raw sockets which don’t need any third party driver, but requires the tool to be run as administrator. WinPcap is still an option if you have it though, as is the Network Monitor Driver by Microsoft.
1. Using HTTPNetworkSniffer is very easy, simply start the tool and it will ask you to select the network capture method of Raw, Winpcap or Microsoft Network driver, and the network adapter if you have more than one installed. Then click OK.
2. The program will start capturing automatically, and you now just need to launch the installer or click the webpage button etc to capture the URL. Then press the stop button and look at the URL column (far right) in the window to locate the executable. Alternatively double click on the entry to get the full URL you can copy along with other useful information. The image below extracts the full offline installer for Freemake Video Converter from its small web installer.
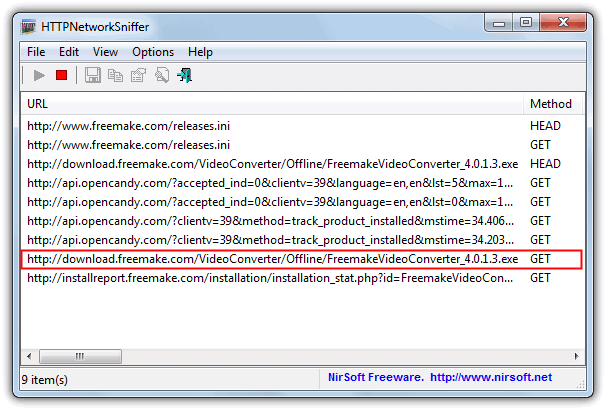
A handy thing about HTTPNetworkSniffer is it shows a lot of other packet information columns such as host name, method, user agent, response code & string, content type, referrer, encoding, content length, connection and much more. All columns can be turned on or off via the View menu.
If you want more than just the sniffing of HTTP requests and responses, then another NirSoft tool called SmartSniff is like a more advanced version of HTTPNetworkSniffer. It can also handle sniffing other protocols such as UDP, ICMP, SMTP, POP3 and FTP while providing other functions such as hex dumps etc.
3. Free HTTP Sniffer
If you want a simple to use packet sniffing tool to capture file URL’s then Free HTTP Sniffer is a useful program to look at. There are no advanced options which means it doesn’t clutter up the window with useless information. One or two minor issues are the donate nag on start and the WinPcap driver included is out of date for newer versions of Windows, so you will need the latest installer from WinPcap.org or there will be an error on launch. Usage is very easy:
1. Start Free HTTP Sniffer, click Options and select “Only addresses sent by any computer” for the Sniffer Mode. This step isn’t strictly necessary but will cut down the useless information in the window even further.
2. Press the Start button and launch the web installer or executable etc. When the file you’re looking for has downloaded, click Stop and look in the main window for the file that looks like the correct one.
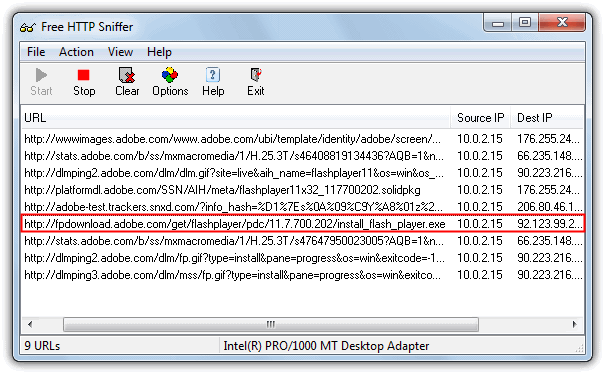
3. Then you can double click on it to try the file in a browser or go to the File menu and save all the URL’s in the window to a text file. As you can see in the screenshot above, it was very easy to find the Adobe Flash Player full executable we also found in URLSnooper. The network adapter can be changed from the File menu.
4. Socket Sniffer
Socket Sniffer is another very easy to use tool to sniff a URL from a web installer or webpage. While getting the program running and capturing packets takes no effort at all, interpreting the results is slightly more tricky because it mixes in UDP and ICMP protocols as well as TCP which will be where you find any file URL’s, so it takes a tiny bit more searching of the results.
1. Socket Sniffer is portable so you simply run the standalone executable. It appears to run using raw sockets as no third party drivers are required. Select the IP address of the current network adapter from the top left drop down menu and then click the Start Sniffing button.
2. After running the web installer or setup file etc, stop the sniffing and browse through the TCP protocol entries by clicking on them and looking at the results in the lower pane.
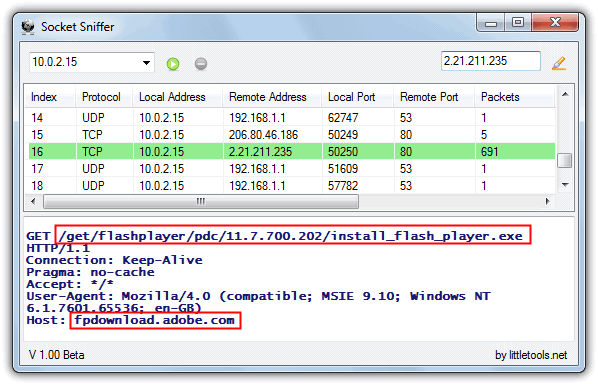
3. You should find an entry with a GET that appears to be the path and file name of the full installer. To get the full URL to the file you have to take the Host name and append the GET path, so the above would be:
fpdownload.adobe.com/get/flashplayer/pdc/11.7.700.202/install_flash_player.exe
Socket Sniffer requires the .NET Framework 2 or above to run.
5. PacketViewer
PacketViewer is another portable tool to sniff out TCP packets from the TCP, UDP or ICMP protocols. It also has a few options to help narrow things down such as an IP address and port filter for both incoming and outgoing packets, and the most important filtering option of entering a string to filter the packet messages. Using this we can filter out everything apart from executable URL messages.
1. Run the portable PacketViewer.exe and go to Options. Untick Message Filter > No Filter and put .exe into the text box, then click Apply and Close.
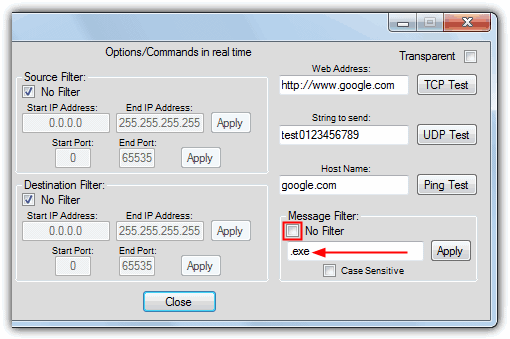
2. Then after clicking Start run the web or setup installer and then stop capturing after the main file has downloaded.
3. Looking through the captured entries should be easy because only packet messages containing .exe will be displayed, then you need to append the GET path details to the Host address like the Socket Sniffer tool above. PacketViewer can also automatically save every capture session to a log file.
These tools simply won’t work unless other essential components have been installed first.
WinPcap is usually installed automatically if not present, but even that is not sufficient for the sniffer tools to work. For instance, try to use URL Snooper with a VPN connection; it fails… unless the Network Monitor Driver is installed. And I only tested this in Windows XP.
Use NetPeeker. This also gives you a detailed information of all the network connections with the option of blocking individual connection. Really good!
These tools saves a lot of internet usage and time wasted to install softwares with a web installer. After getting the link I use IDM to download them.
thank you ..It’s crazy I have been downloading adobe stuff and getting extra..
This will be of great help.
really! nice one
I have been using Url Snooper quite a long time and I can highly recommend it to everyone.
Thank you for mentioning the program Raymond — I’m glad you find it useful.
-mouser
Thanks very much ! ;)
Great tricks.
Thank you Raymond.
good information to have, thanks Raymond.
nice info.
a real great writeup mate, thanks!
Thanks , very useful tools
Thank you! It’s really useful :)
nice input..:-)
Thank You So much Raymond.
Nice Trick to find Url
Thats Exactly what I needed. Now i can have manual setups and install without even connecting.
Thanks a ton Raymond.
Outstanding, in this way, we can also sniff streaming channels link and then play them in VLC. Nice article. Thanks Raymond, you are the best… Raymond Rocks.