Anti Screen Capture Software: Best Picks in 2023
Testing AntiKeyloggers with Real Keyloggers
To find the best anti-keylogger software and also to determine the effectiveness of Zemana AntiLogger, SpyShelter Premium and DataGuard AntiKeylogger, we’ve tested them against 12 different malwares (7 commercial keyloggers + 5 RAT Trojan) that are capable of logging keystrokes & the clipboard, taking screenshots, activating the webcam and capturing audio through a microphone.
- Invisible Keylogger Stealth
- Elite Keylogger
- REFOG Keylogger
- All in One Keylogger
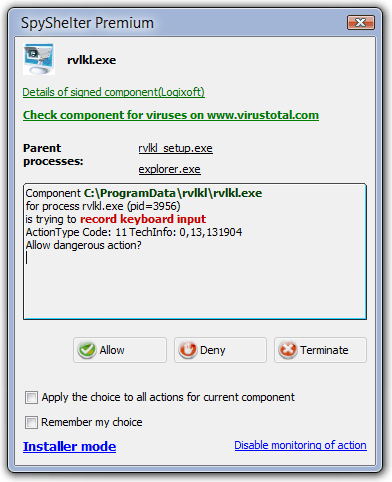
- Revealer Keylogger Pro 2.0.8
- Advanced Keylogger 3.1.1.205
- Award Keylogger Pro 3.3
- Bozok 1.4
- DarkComet 5.3
- CyberGate Excel 1.3.6.0
- Lost Door 8.0.1
- NetWire 1.4c
Zemana AntiLogger and SpyShelter Premium are tested in Windows 8 Pro 32-bit while DataGuard AntiKeylogger in Windows 7 Ultimate 32-bit because it doesn’t support Windows 8. All Windows operating systems are fully updated during the time of testing.
In the interest of getting the fairest and most accurate results, we’ve used imaging to restore Windows back to the same state after each and every test that was conducted. This rules out possible conflicts and guarantees that each protection module is tested in the exact same Windows environment. For example, Zemana was installed, the keystroke test was performed for Invisible Keylogger Stealth, then the system was reset again for the next test and Zemana installed again for the Keylogger Stealth install test, and so on…
Test Notes for Zemana AntiLogger
1. Zemana seems to have a serious bug where all modules must be enabled for the protection to be active. For example, if the Anti-ScreenLogger is enabled but Anti-KeyLogger disabled, the hacker can still capture your screen. However when turning on Anti-KeyLogger, Zemana then detects the screen capture. The same thing happened when we only enabled System Defense but the rest of the protection modules were disabled, the keylogger is able to install without Zemana detecting any injection. So if you’re using Zemana AntiLogger, make sure that all protection modules are enabled.
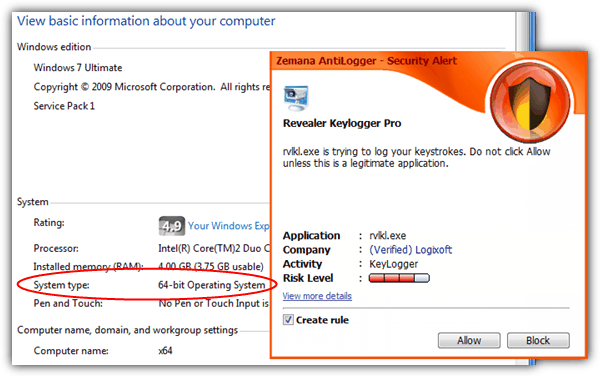
2. There are some people claiming that Zemana AntiLogger doesn’t work on 64-bit (x64) Windows. We were curious to find out if it is true, so we activated the keystroke logging from Revealer Keylogger Pro on Windows 7 Ultimate 64-bit and Zemana AntiLogger instantly block the action and display the security alert popup.
3. Other than the behavior-based protection, Zemana AntiLogger offers an additional protection called IntelliGuard Cloud where it checks the files that you want to run with their servers to determine if it is safe or automatically blocking it if it is a known malicious file.
Test Notes for SpyShelter Premium
1. SpyShelter’s alert window hung a few times when detecting suspicious logging activity.
2. SpyShelter’s System Protection (HIPS) is very sensitive, notifying you of any activity with an alert popup. This is because the “High security level” option is selected by default to offer better protection rather than the medium security level with decreased alerts.
3. There is an option in Settings to allow/prevent SpyShelter from being terminated via Task Manager. Although it is not possible to terminate SpyShelter’s process from Task Manager after unchecking the checkbox, we were still able to kill the process using a third party task managing program called Process Explorer.
Test Notes for DataGuard AntiKeylogger
1. DataGuard AntiKeylogger was last updated on March 2011 and does not work on Windows 8. Even the links to purchase a license via Plimus are unavailable.
2. When DataGuard detects malicious activity such as keystroke logging, it will automatically add the process to the “Auto-detected modules” which will block other supported logging activities. However if the program is signed, the activity will be allowed. Certificate checking can be disabled in program’s Advanced Options.
3. DataGuard adds Explorer.exe to Auto-detected modules causing the Windows explorer to crash.
The table below shows the detection result of each logging behavior from all 12 keylogger program. The red colored “NO” means that the logging behavior is not detected while the blue colored “YES” means that it is detected by the antikeylogger.
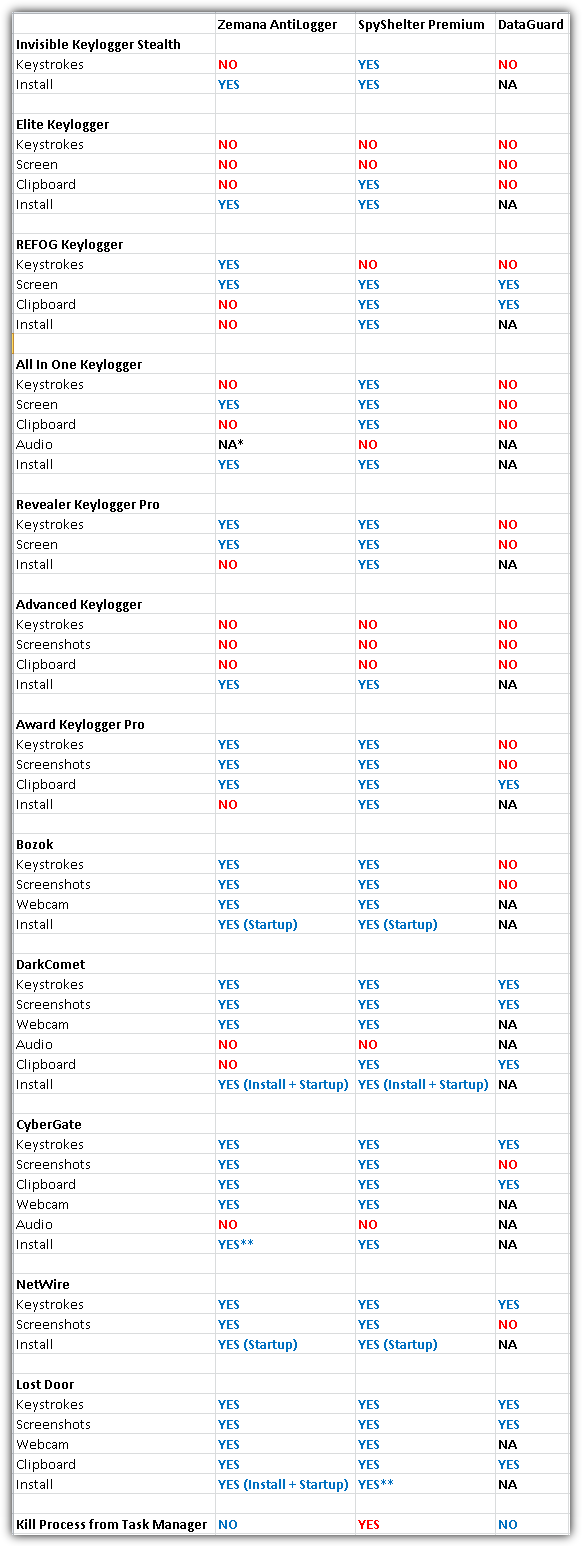
* Unable to Test. Zemana kept on detecting injection.
** YES (Even without Install & Startup)
As you can see from the test results above, none of them are perfect in detecting every attack method but SpyShelter and Zemana came close.
We found that it’s possible to evade the detection from these anti keyloggers by not automatically adding the keylogger itself to Windows startup and making sure that the malware does not activate an offline keylogger. This will allow the hacker to gain a one time access to disable or tamper with any running security software and then followed up by manually adding a startup entry for the malware. During that time, the hacker can also download your files from your hard drive with a file manager found in most remote access tools. This is when you will need file encryption to keep your important files safe.
I know the subject old but I had to react ,@or rex I do not know whether to laugh or to cry from such nonsense, spyshelter is from Poland!
Have any of these been verified to work against this attack?
“In the attack seen by FireEye, the rogue shim database masqueraded as a Windows update”
Security researchers from FireEye have recently seen the shim technique used by a group of financially motivated cybercriminals known in the security industry as FIN7 or Carbanak. Since 2015, this group has stolen between $500 million and $1 billion from hundreds of financial organizations worldwide.”
SpyShelter made in germany
When you remove it from your computer
It is not really erased
But continues to work
And sends data out
Thanks for article
Why you put SpyShelter at second place since it’s much more effective than Zemana?
Second: Why screenshot from SpyShelter has 5 years? Program has updated GUI from the long time.
The article is from 2013 and back then Zemana was better in this test.
Hi, I’m doing research to secure my devices and came across this article. Sometimes, I have to share access of my laptop with friends for work purposes. But I only give them access to a non admin account. Is there a key logger program that can be installed on a non admin account and then be activated for all users? If so, how can it be prevented? Otherwise am I safe by just giving them access to a non admin account? Thanks for reading. Kindly please reply.
Just installed zemana and can not see anti-screen, anti-webcam logger etc.. as shown on your picture. RAYMOND
That is because Zemana recently underwent a major change between version 1 (which is in this article) and version 2. It is now more of a general anti malware tool than a dedicated anti logger/screen/cam software.
Good afternoon,
Please, do you speak whether the spyshelter to exist free for the version 64 bits, plataform windows 10?
thank you.
SpyShelter 10.1 Free Anti Keylogger – works now for free with 64 bit systems!
I like this blog loving always
SpyShelter is far more better than Zemana….has more alerts but has also much more protection.
Hi Raymond,
I am well aware that this test was created some time ago, but my question is if you will update your test with other/more anti-logger softwares. I would be specifically interested in seeing how Key Scrambler performs compared to SpyShelter and ZAL.
BR
KF
The SIVD Player is great for preventing screen capture of video content while it being played..
You’re BACK!!!!!!!!!!!
man, i hope you can make it a weekly thing ;)
They are good but i don’t like too many software running on my pc so i simply uses sandboxie.
Thanks for the nice article :)
I was thinking about screen capture by proxy. Zemana allows windows snipping tool. Can a malware not pass zemana by simply making calls to snipping tool without showing its window and storing the snaps in a secret folder. It could then send these to an attacker.
I wonder if that scenario has been considered.
Besides @Brand says that – Just a heads up – Zemana doesn’t block any kernel/service level loggers (these are most advanced and dangerous) under 64 bit systems.
Is there any evidence for that ?
Raymond,
I read the discussion about your testS on wilderssecurity.com and I think I understand better now.
In fact you did two tests.
One (traditional) protection test, the one which (quite) everybody expected : the antikeylogger is already
installed on the computer and you try to install and run the keylogger.
The results of that test are in the “install” lines.
In that case, SpyShelter detects and block ALL the keyloggers; ZAL fails a little more.
So both are -still…- very good on the contrary of what I firstly understood.
This is a good news ! And perhaps I am not alone to have misunderstood it.
Then you did another detection test : you deactivate the antikeylogger and install the keylogger so that no
(block or allow) rule is created. Then you launch both the keylogger and the antikeylogger and you see if this last one is able to detect and block the logging actions of the keylogger.
The results of this test are all the others except “install”, if I am not wrong.
This is an interesting and useful test to give an idea about the limit of the protection of the antikeyloggers.
Hey Raymond,
Great site and that’s great news about the Zemana (excellent software; I recommend it to everyone) promotion.
Thank you Zemana & thank you Raymond!
Best,
Bob
Just a heads up – Zemana doesn’t block any kernel/service level loggers (these are most advanced and dangerous) under 64 bit systems.
Zemana is able to detect all the malicious programs.Zemana is the best.
I tested Zemana Antilogger with the mentioned malicious programs above on 8 32 OS and different OS’s more.
Raymond,
I am a little disappointed with the results of ZAL and SpyShelter.
I remember you wrote something like : “Believe me or not, ZAL can detect ALL keyloggers”.
Times are changing and it is better to know it. Thanks to you.
Zemana is the best….it works fine on my Win8.1 x64 PC……..
Please review Oxynger KeyShield. It Is a anti-keylogger virtual keyboard with screen capture and mouse logging protection. It is also free.
Thank you, Iove it.
You say the test is done on Windows 8, but not whether it is 32 or 64 bit.
Thanks for asking. We’ve tested it on Windows 8 32-bit and added the bit to the post.
I tested Zemana Antilogger with the mentioned malicious programs above on 8 32 OS and different OS’s more. The results do not seem like yours. it almost do not miss all monitoring activity done by these programs. So it is quite good.
To test EACH protection module individually on Zemana is not as easy as it seems due to a bug that I’ve mentioned on the article.
Zemana is able to detect all the malicious programs IF all of the modules are enabled, but that would defeat the purpose of our test in determining if each individual logging behavior can be detected. We had to go through the trouble in customizing the malicious program to run only 1 logging activity at a time.
I’m afraid that Zemana completely fails tests under 64 bit systems – I have just checked.
Who even uses 32 bit systems nowadays?
You can’t say completely. Read the 2nd point of my test notes on Zemana. I even have a screenshot to show that Zemana installed in Windows 7 64-bit detected keystroke logging by Revealer Keylogger Pro.
[Who even uses 32 bit systems nowadays?]
Did you even think before you made that statement? Just because you saved up your milk money and have a bright shinny new computer, doesn’t mean the world as a whole, is as lucky as you. Only in the USA, are 64 bit systems thought of as being better. In reality, if you were familiar with the architecture of a 64 vs. 32 bit system, you would like me, put the 64 back in the box and hope some sucker comes along and buys it from you. /Oct2013/.
thanks for the test, I’m glad that you found so many hole in the protection.
it gives me some new strategy for keylogger protection
Nice share :D
Whats your opinion on adding QFX Anti Key Scrambler into this? does it adds more protection?
Can any of these key loggers are capable of captruring virtual keyboard input?
QFX KeyScrambler does provide added protection since it is a different method in fighting keyloggers. Refer to this article for keystroke encryption test: https://www.raymond.cc/blog/keystroke-encryption/
Virtual Keyboard test will be next on another article. Stay tuned.
Doesn’t Kaspersky PURE or Internet Security help us to avoid keyloggers and captures?
It does, but not all which is why it would be better to have a second line of defense.
I thought they both really slowed down my PC (when running both), so after licence expired I removed it and stayed only with KIS.
Raymond!
I decided to check on the website to see if there was any updated information . . . and Voila!
(You posted something new just 5 hours ago – – and a Very interesting article it is.)
I hope we can continue to go to your Blog and learn something from You and guests – – WELCOME BACK!
Thank you for Sharing & Caring
TheRube)
Not easily discerned from their Web site info, the full feature set of AntiLogger “Paid” is available only for Win8; otherwise Free and “Paid” must run concurrently. From a July 24 reply from Zemana to my inquiry: “The encrypting function of AntiLogger is active on only Windows 8 64 bit. However, this function on AntiLogger Free is active on all OS’s. The encrypting function of AntiLogger will be active on all OS’s very soon. For now, we suggest our customers who use another OS except Wİndows 8 64 bit to use both of AntiLogger and AntiLogger Free at the same time.” As of today’s 1.9.3.503 update, this has not yet been realized. This is not to be misconstrued as a slam – I’ve been using ZAL for years. Thanks Raymond, great review!
Thank you for doing your homework (better than I). I, too, have been using ZAL (paid) for years and became so confident that I just set-it and forgot-it, never imagining that such a serious *flaw* exists in their flagship product. I cannot be as generous as you — they should be slammed for not making the information you dug out more easily available. Well, their Customer Support is great, anyway. :)
Great post.
Hmm, the results are obvious, i wouldn’t have worried if all of them failed. In my opinion the best defense a user can have is common sense. Just don’t use or open untrusted softwares and always take precautions. This has worked for me for years.
Well really nice test raymond.
Thank you Raymond, for the informative review.
Another great article from Raymond. Very informative. Thank you
Hey Raymond! Thanks man!